
[WARNING] This blog post is created when Microsoft Windows still came in a physical box with multiple installation disks.
Microsoft released a new detection this month for Microsoft Defender for Identity. The detection detects “Suspected Kerberos SPN exposure,” which is an attack called Kerberoasting. This blog post will briefly explain what a Kerberoasting attack is and how to mitigate it.
Kerberoasting is not a new attack. The detection by Microsoft Defender for Identity is, though. People like harmj0y, Sean Metcalf, and many others documented Kerberoasting well, but since the detection is new in Microsoft Defender for Identity, I will briefly go through the attack.
Kerberos
To understand Kerberoasting, we first need to know how Kerberos works. Kerberos is an authentication protocol based on tickets. The protocol is an authentication protocol developed by MIT and adopted by Microsoft since Windows 2000. Kerberos is also complicated and hard to secure.
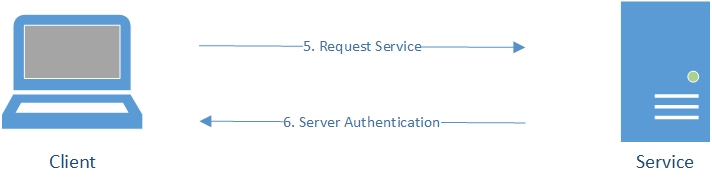
For a client to access a service (a SQL server, a web server, a network share, etc.), the client needs to authenticate and request a Ticket Granting Service (TGS) ticket from the Key Distribution Center (KDC). The Key Distribution Center exists of two components: the Authentication Service (AS) and the Ticket Granting Service. Within a Microsoft environment, the Key Distribution Center is the Domain Controller. With a valid Ticket Granting Service ticket, the client can access the requested service.
Here is an oversimplified overview of these ticket requests:
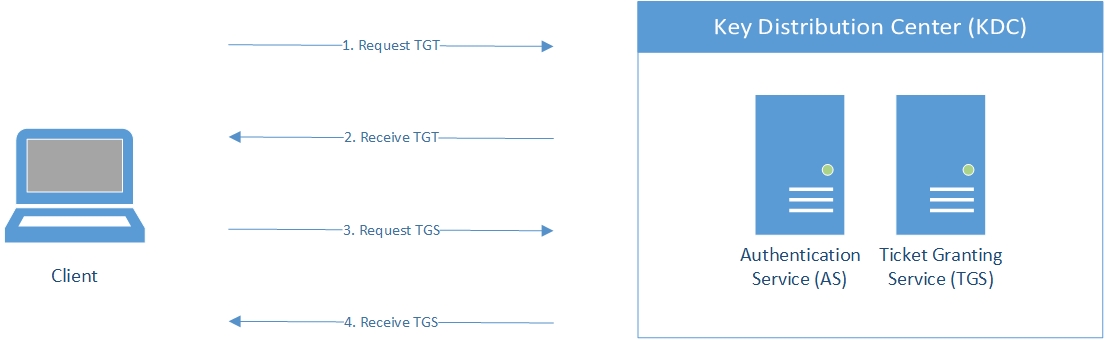
First, the client needs to authenticate. The Authentication Service handles the authentication. The client sends a Ticket Granting Ticket (TGT) request and encrypts the timestamp in the request with the users’ password hash. Active Directory holds the password hashes of all users. If the Domain Controller can decrypt the request and validates the user authentication, the Domain Controller sents a valid Ticket Granting Ticket.
With a valid Ticket Granting Ticket, the client can now request a Ticket Granting Service ticket. This part is essential: Anyone with a valid Ticket Granting Ticket can ask for a Ticket Granting Service ticket. The Ticket Granting Service ticket is encrypted with the hash of the user’s password the service belongs to (the Service Principal Name property within Active Directory on the object).
With a valid Ticket Granting Service ticket, the client can access the requested service.
Kerberoasting
Now that we know how Kerberos works in a nutshell, we can take a look at Kerberoasting. Remember that the Domain Controler uses the users’ password hash to encrypt the Ticket Granting Service ticket. Suppose an attacker requests a Ticket Granting Service ticket and uses a password list to brute-force the ticket, and the password is weak enough. In that case, the attacker can figure out the password by brute-forcing the ticket and obtain the password for that user. This attack is called Kerberoasting.
There is an option to enable a more robust encryption algorithm in Active Directory on the user object hence harder to brute-force:
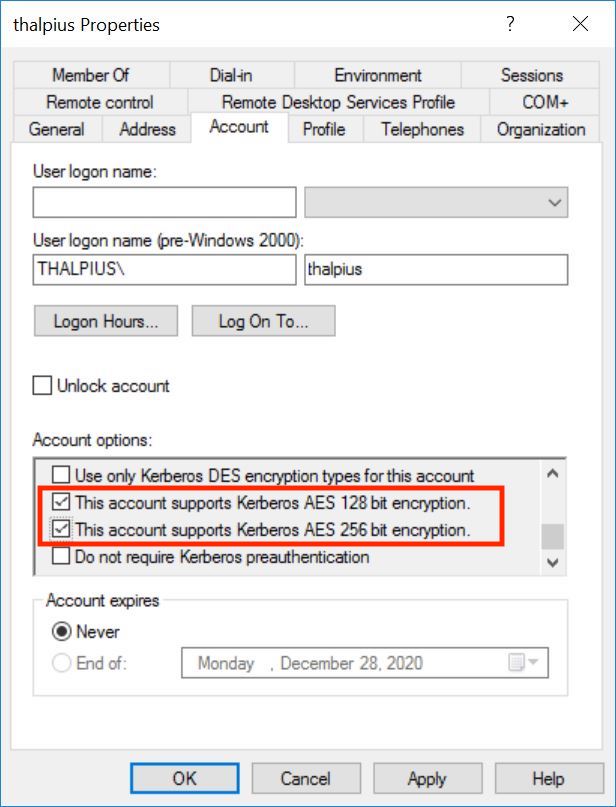
Unfortunately, this option is only to support AES. If an attacker requests an RC4 (weaker encryption) encrypted ticket, the Domain Controller still sends a ticket with RC4 encryption, which is easier to brute-force than AES.
Mitigation
Since the ticket needs to be brute-forced, a strong and complex password is the best mitigation for this attack. Even if the ticket can be requested using RC4 encryption, a generated and lengthy password is hard to brute-force. Use a generated and lengthy password for all service accounts that contain a Service Principal Name.
If Microsoft Defender for Identity detects a Kerberoasting attack, reset the password for the user account, and isolate the machine where the attack takes place. Investigate for malicious activities once mitigated the attack on the endpoint.
Note: Microsoft Defender for Endpoint contains an option to isolate the device. You will be able to reconnect the device back to the network at any time. The button on the device page will change to say Release from isolation, and then you take the same steps as isolating the device.
Conclusion
Kerberoasting is an attack a lot of attackers use because it is beneficial and hard to detect. Now that Microsoft Defender for Identity detects Kerberoasting it is a good start. Hopefully, other Kerberos attacks will get detected by Microsoft Defender for Identity soon.
I have created a small C# project that requests a Ticket Granting Service ticket using KerberosSecurityTokenProvider to use for Kerberoasting. I started the project for educational purposes only, but the tool works fine and is not detected by Microsoft Defender for Identity.
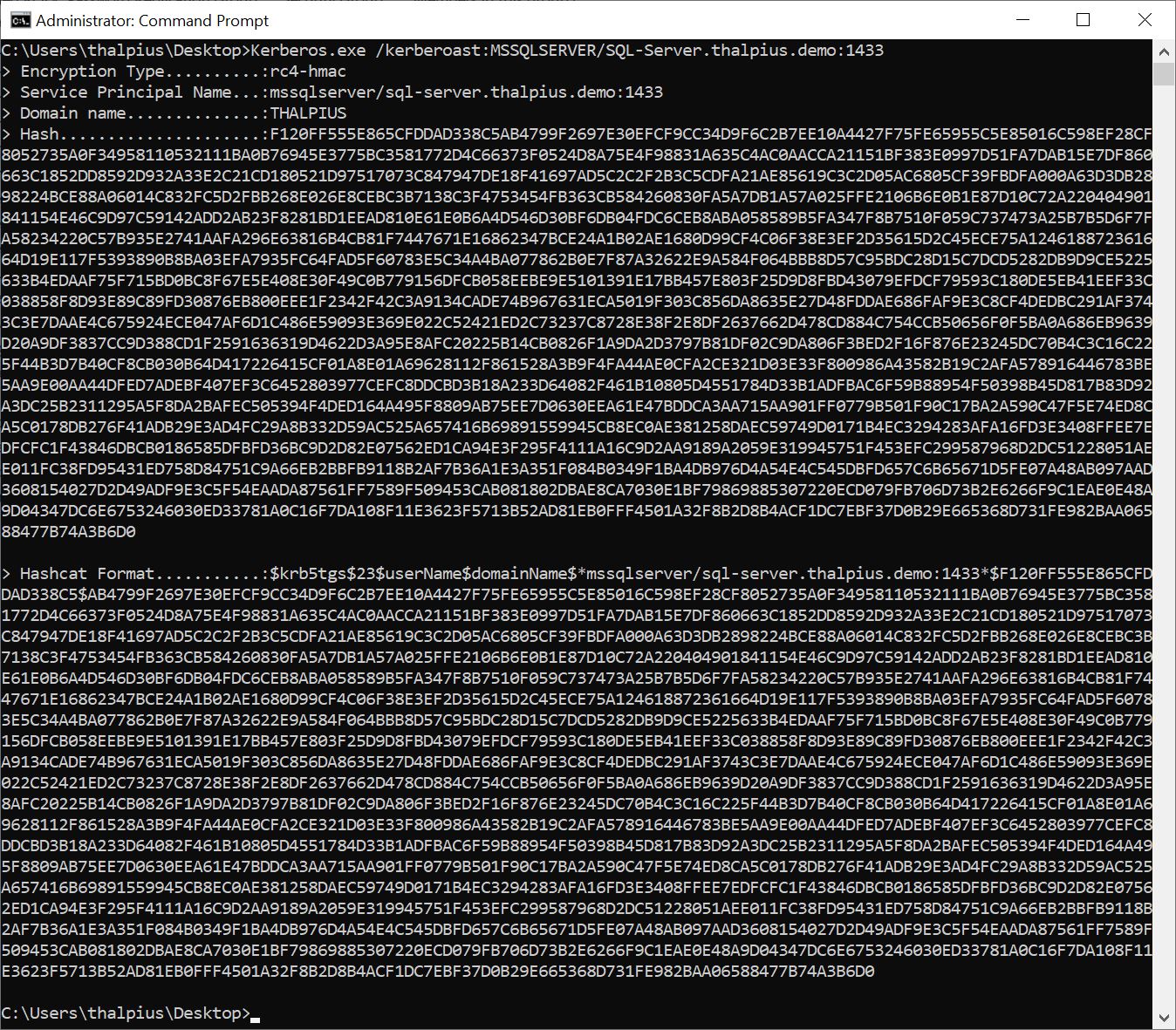
The tool can be found here.