
[WARNING] This blog post is created when Microsoft Windows still came in a physical box with multiple installation disks.
Microsoft announced four new detections in Azure Active Directory Identity Protection last month. One of the four detections is “Workload Identities Leaked Credentials.” During a Microsoft webinar where I demonstrated this new feature in Microsoft Identity Protection, multiple people requested the tool I created, so I decided to release it.
This blog post will briefly explain the new Workload Identities Leaked Credentials detection and link to a tool I created to scan GitHub repositories for leaked credentials, specifically AadSecrets using the GitHub API requested by some people during a webinar.
Workload Identities Leaked Credentials
Azure Active Directory Identity Protection is a risk-based feature to protect identities in the cloud based on many indicators (atypical travel, malware-linked IP address, and many more). Conditional Access uses these detections to prevent an identity from accessing cloud services based on risk classifications. Using Azure Active Directory Identity Protection makes it possible to mitigate an attack within seconds due to an automated response.
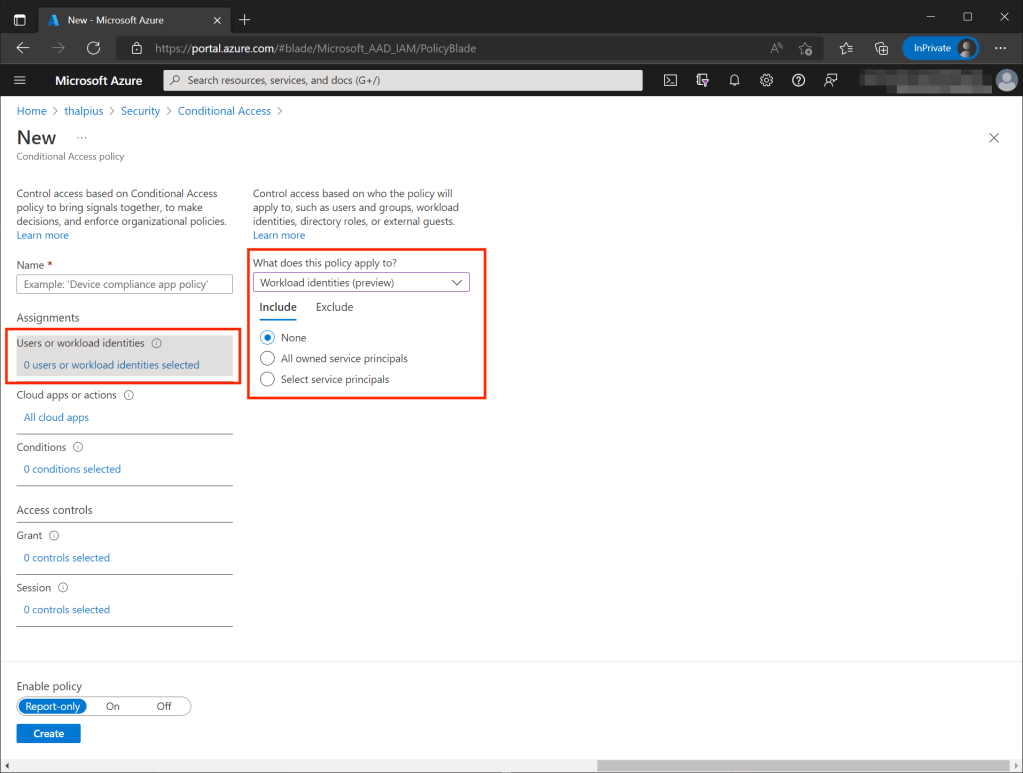
Note: Conditional Access policies, at their simplest, are if-then statements. If a user wants to access a resource, they must complete an action. An action is forcing the user to use Multi-Factor Authentication or forced to change their password.
The new feature in Azure Active Directory Identity Protection now supports the detection of leaked credentials for workload identities. A workload identity is an identity used to authenticate and access other services and resources. Think of a Service Principal created when you create an Enterprise Application.
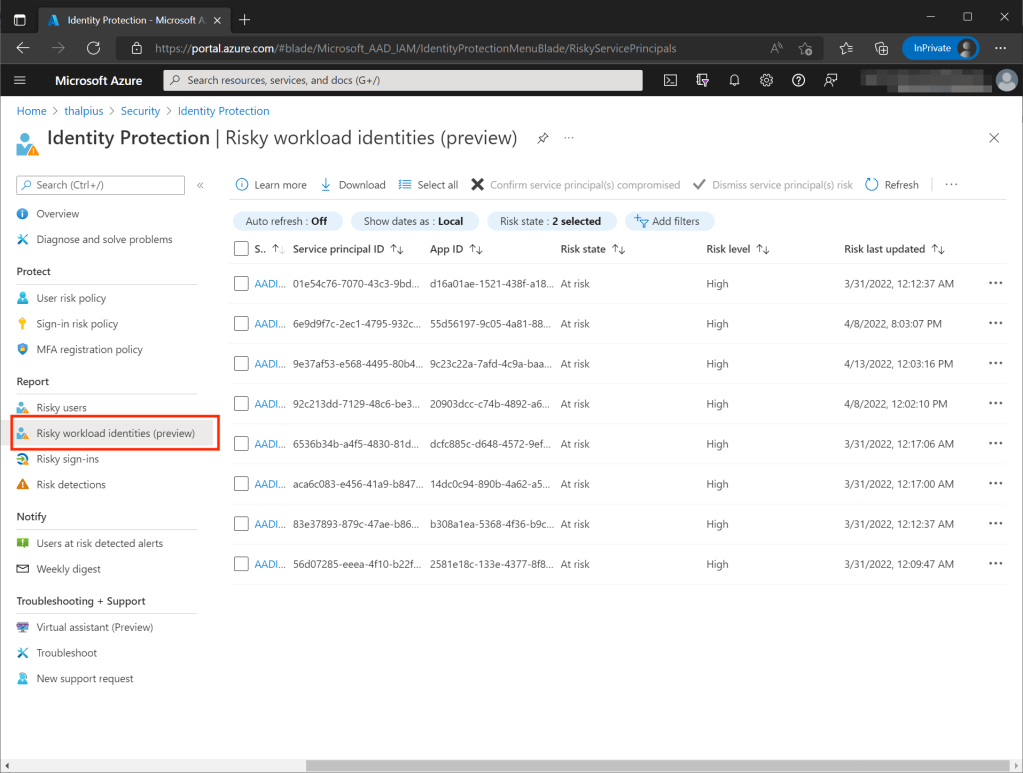
Microsoft scans GitHub, Pastebin, etc., for leaked credentials, and if there is a match with your environment, by comparing the hash of the password, it will trigger an alert and mitigate the risk.
Leaked credentials are a common mistake made by many administrators. GitHub already supported the “Leaked Credentials” feature, but no comparison in any environment occurs. Still, with Azure Active Directory Identity Protection, the hash is compared with the hash in Azure Active Directory to see if there is a match. Suppose there is a match, an alert triggers.
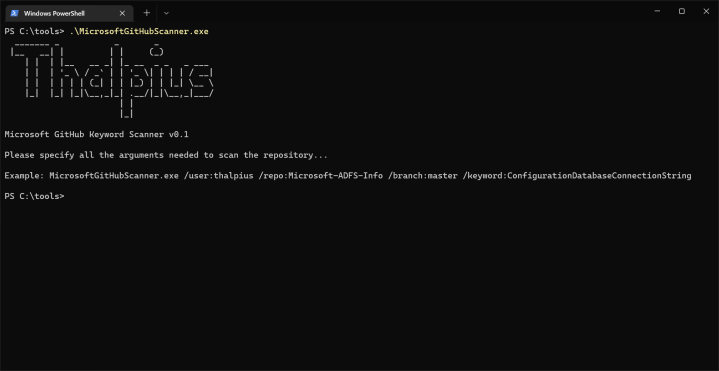
Microsoft GitHub Scanner
For demonstration purposes, I created a tool to scan for leaked credentials on GitHub. The tool uses the GitHub API to get all files in the repository and scans for AadSecrets. As I created it for demonstration purposes only, it is not perfect. PowerShell could be an option, but I decided to use C# core for fun.
The tool is simple. I use an API to list all files in a repository and re-write the URL to get the raw contents. Then I scan for AadSecret in the raw contents for leaked credentials. I do not have to download any repository as some tools do to make it simple, fast, and accessible.
Conclusion
In my opinion, Azure Active Directory Identity Protection is a must to protect identities in any corporate environment. The combination of Azure Identity Protection and Conditional Access drastically lowers the risk of a compromised identity. Now that workload identities are also protected makes it even more powerful.