
[WARNING] This blog post is created when Microsoft Windows still came in a physical box with multiple installation disks.
Microsoft Office 365 ATP Attack Simulator is used to determine how end users behave in the event of a phishing attack, and checks for weak passwords within your tenant. In one of my previous blog post, I already mentioned the Attack Simulator, and in this blog post, I will go into the Attack Simulator in more depth.
Microsoft Office 365 ATP Attack Simulator consists of four simulated attacks: Spear Phishing (Credentials Harvest), Spear Phishing (Attachment), Brute Force Password (Dictionary Attack), and Password Spray Attack.
Note: The difference between a Brute Force attack and a Password Spray attack is that with a Brute Force attack, you are trying to log-in on a single identity with multiple passwords. With a Password Spray attack, you are trying to log-in with a unique password on various identities. Microsoft Office 365 ATP Attack Simulator contains both.

Spear Phishing (Credentials Harvest)
Let us take a look at the Spear Phishing (Credentials Harvest) attack first.
A spear phishing attack is a targeted attempt to acquire sensitive information like user names and passwords by masquerading as a trusted entity on a targeted victim. This Spear Phishing attack will use a website to obtain usernames and passwords by asking the victim to log-in.
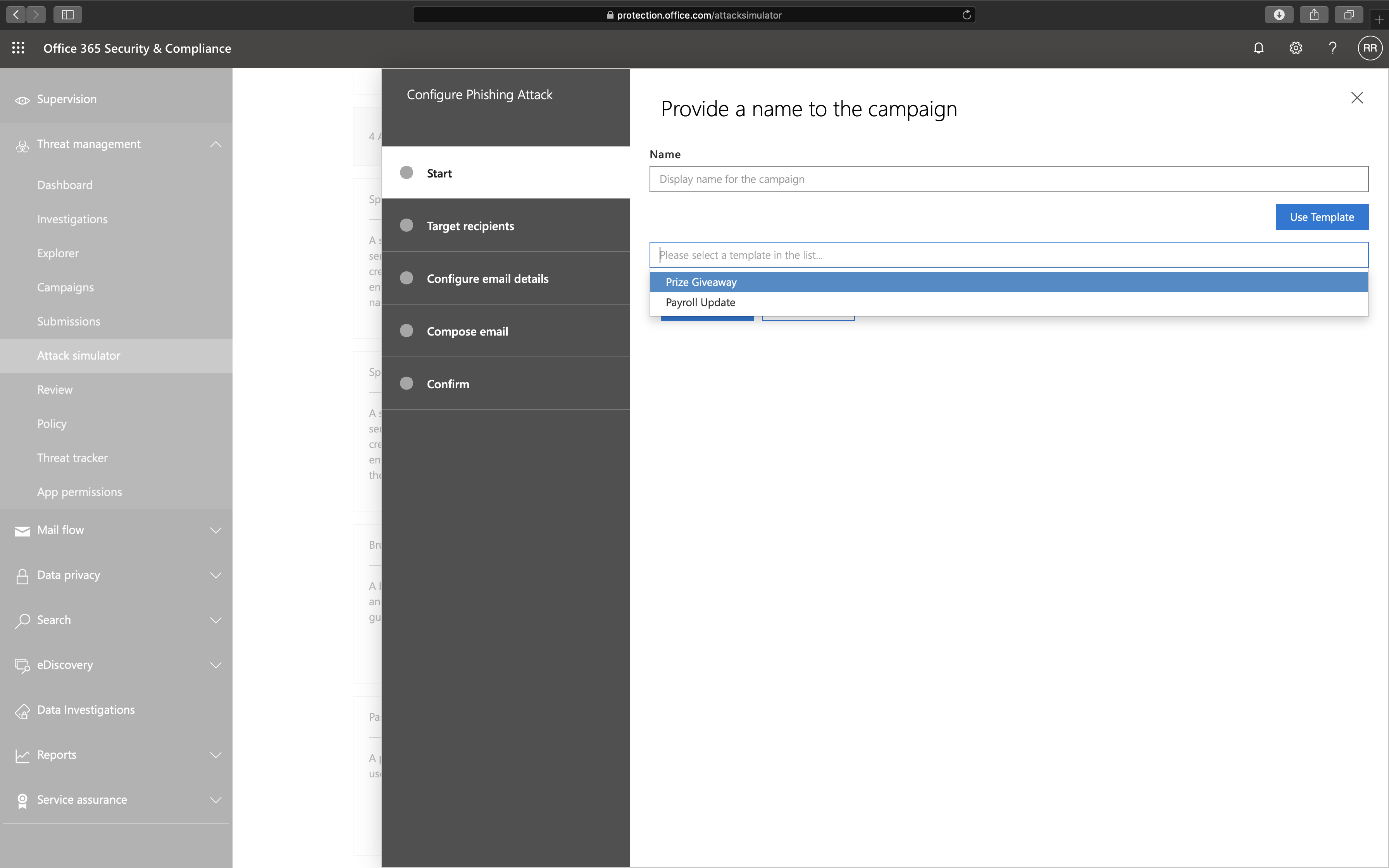
Let us take a look at what options we have if we launch a Spear Phishing (Credentials Harvest) attack. We can use two different templates: Prize Giveaway and Payroll Update, but you can change any detail as well if needed during the wizard.
The next option is to whom we send the phishing e-mail.
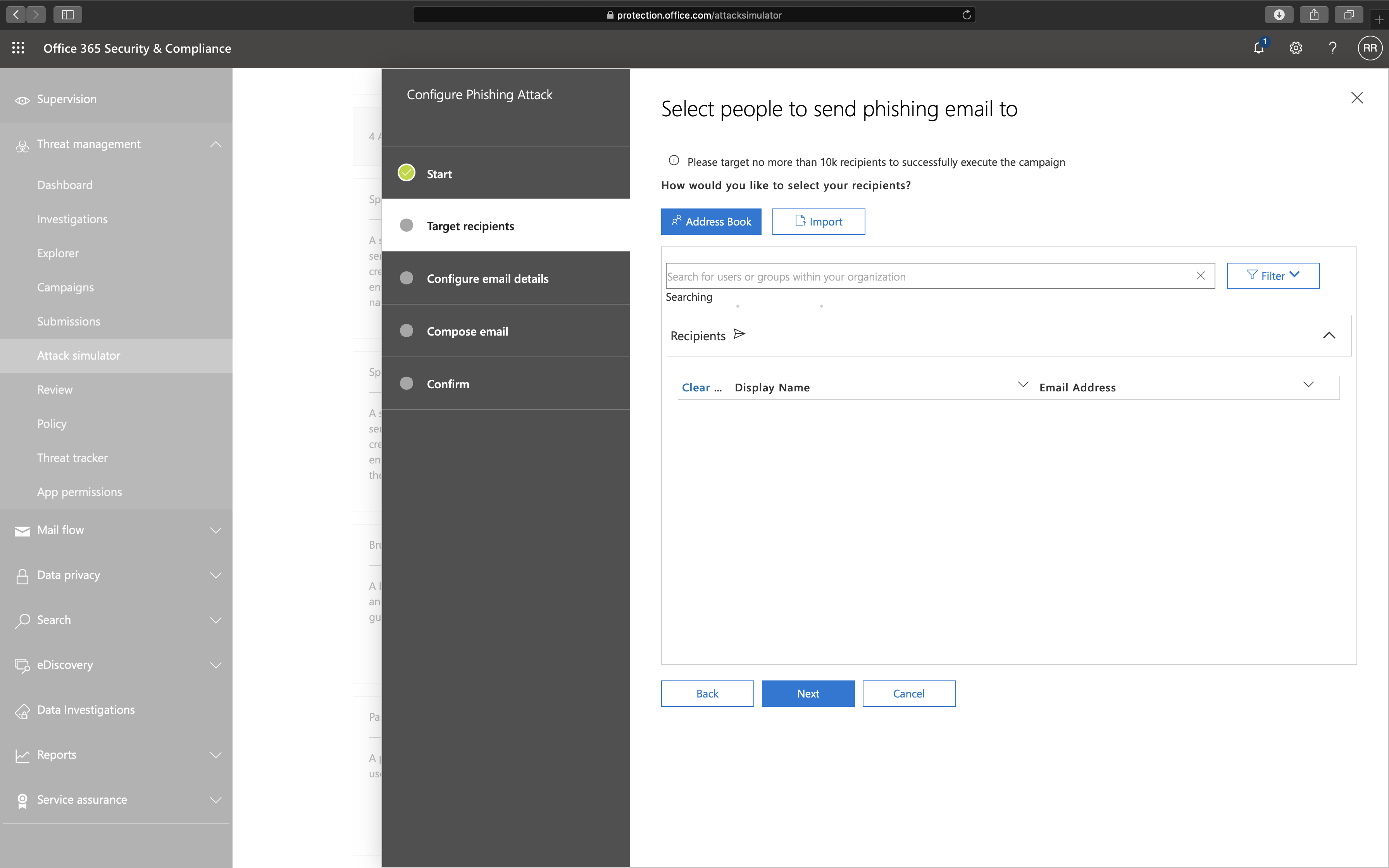
Note: The total recipients that a single campaign can support is 10.000 recipients. You can either select an individual recipient or import a list of recipients.
The next step is to select the e-mail details.
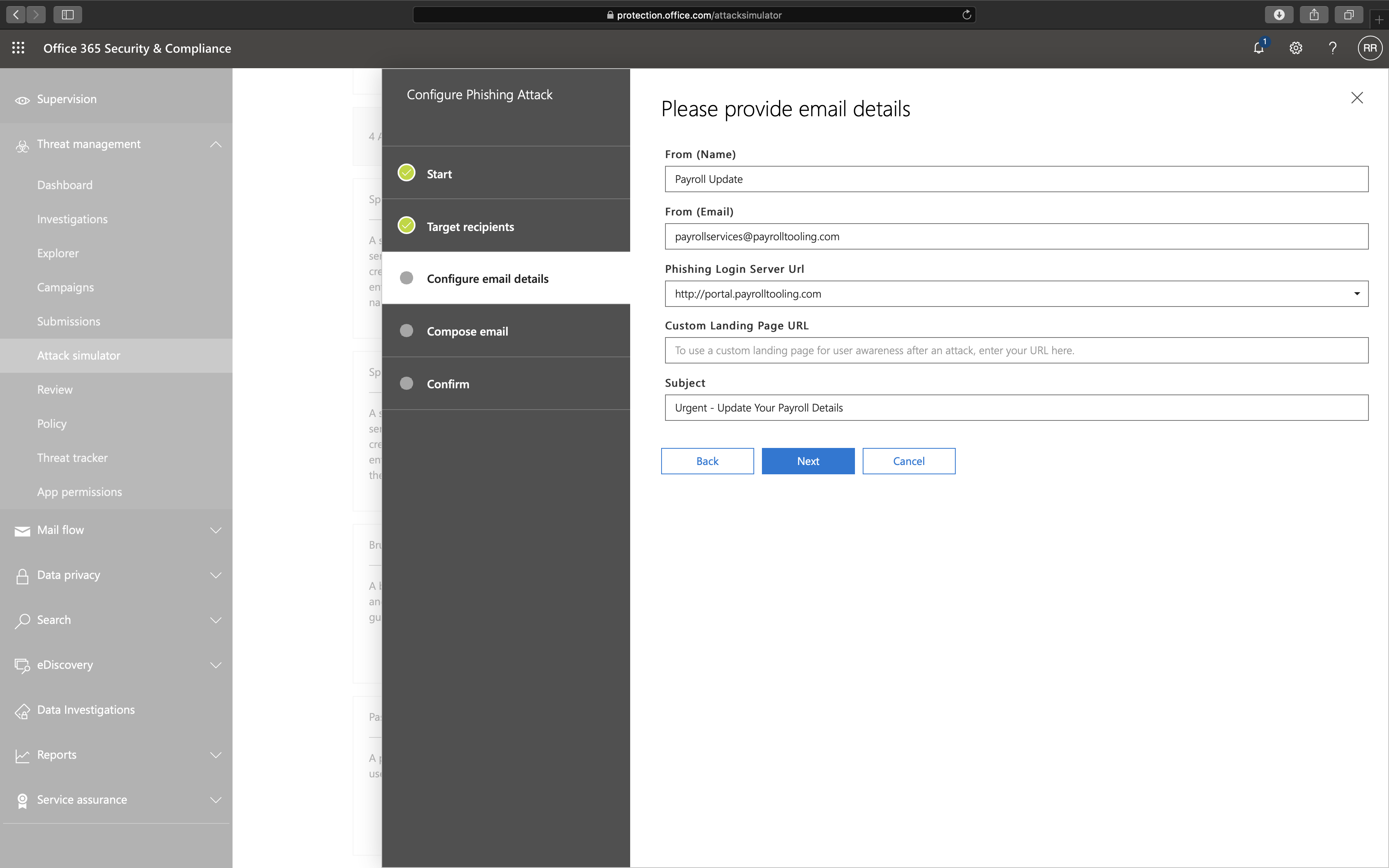
At this moment you can only select a domain from a list as a phishing landing page, which includes:
http://portal.docdeliveryapp.com
http://portal.docdeliveryapp.net
http://portal.docstoreinternal.com
http://portal.docstoreinternal.net
http://portal.hardwarecheck.net
http://portal.hrsupportint.com
http://portal.payrolltooling.com
http://portal.payrolltooling.net
http://portal.prizegiveaway.net
http://portal.prizesforall.com
http://portal.salarytoolint.com
http://portal.salarytoolint.net
The last option which you can set is the body of the e-mail. Since I selected a template at the beginning of the wizard, an e-mail body is already created but can be changed.


The Phishing Campaign is pretty good, and I love seeing this all happening within the tenant. Here is my concern about the phishing campaign though:
- Even though Microsoft uses HTTP on purpose due to security awareness, I think HTTPS should also be supported as phishing websites do not limit itself to HTTP either.
- There is a set of domain URLs that you can choose for the phishing campaign. I would like to see custom domains to make the campaign more realistic.
- The capture portal does not look like a Microsoft Office 365 log-in portal. It would be better to set a custom capture portal (e.q. with a company logo or a copy of an ADFS portal) to make it more realistic or a replica of the Microsoft Office 365 log-in portal.
- The user can log-in to the portal using a user name and password, but there is no multi-factor authentication support. Since Microsoft forces companies to enable multi-factor authentication, support for multi-factor in the phishing campaign would be very welcome.
Spear Phishing (Attachment)
Now let us take a look at the Spear Phishing (Attachment) attack.
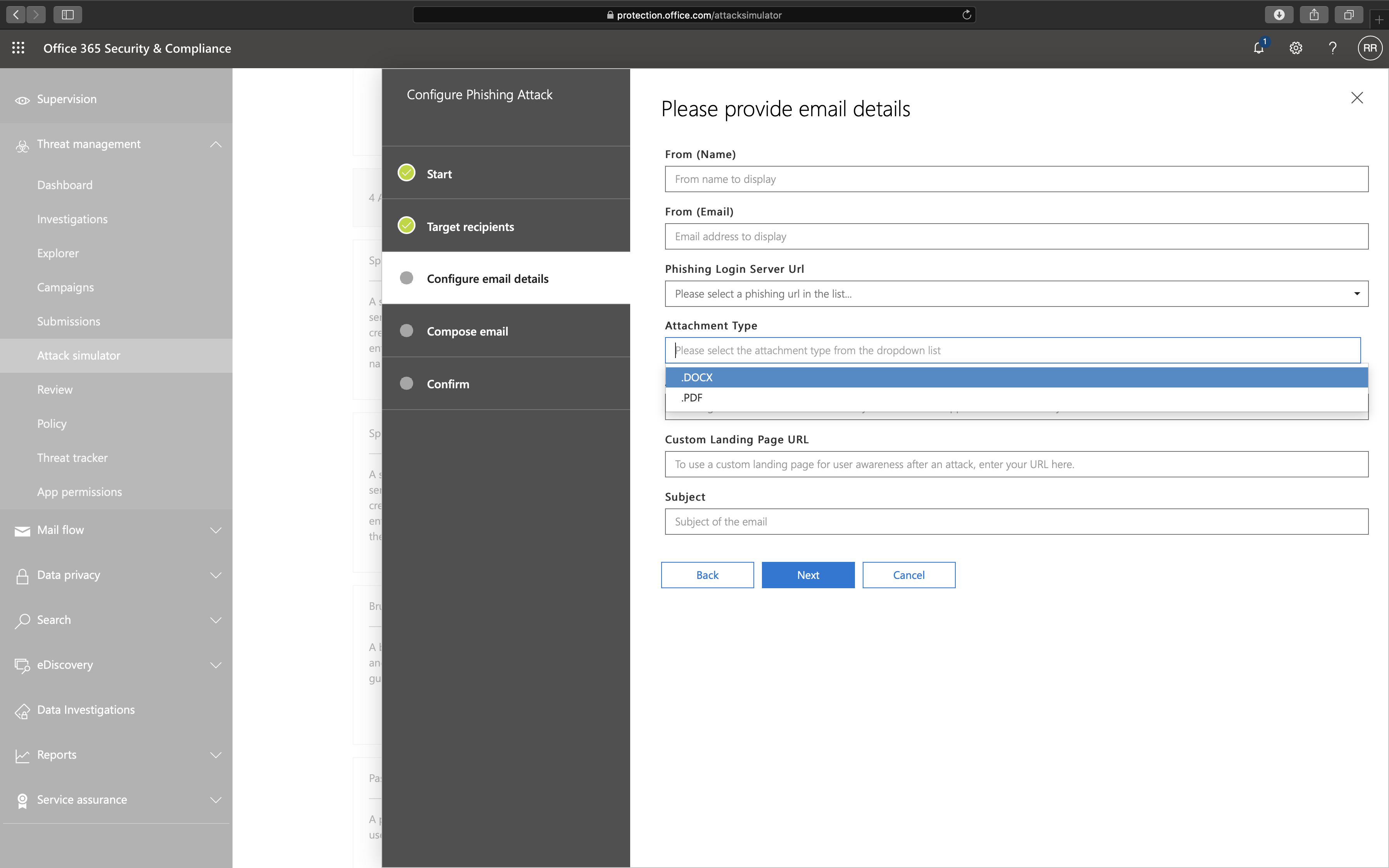
The idea of the Spear Phishing (Attachment) attack is the same as the Spear Phishing (Credentials Harvest) attack except for two options: Attachment Type and Attachment Name.
The recipient will see the following message when opening the attachment:

The recipient also receives a link in the e-mail that goes to a phishing landing page. The idea is the same as the Spear Phishing (Credentials Harvest) attack by forcing the victim to log-in to the portal to steal user names and passwords.
Here I have some concerns as well:
- The attachment does not work when you open it in view mode. If you open the attachment in view mode, Attack Simulator does not notice it.
- The attachment does not contain anything malicious. I would love to see a Word document with a macro as a malicious attachment for the attack to be more realistic.
Brute Force Password (Dictionary Attack)
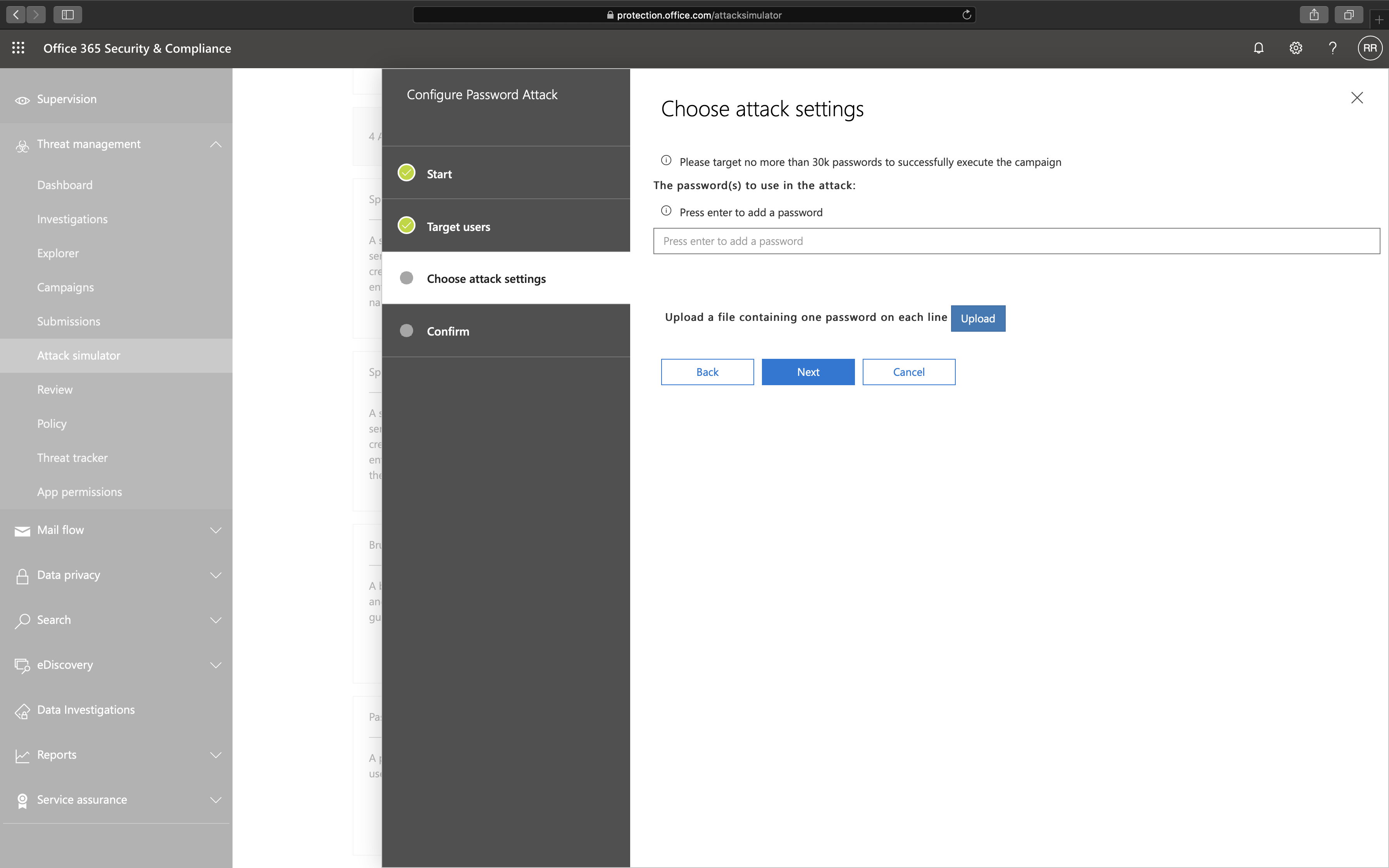
The idea behind a Brute Force Password attack is to try to guess a password for a single identity using as many passwords as possible.
I have some concerns here as well:
- This Brute Force Password (Dictionary Attack) attack or the Password Spray attack does not work when multi-factor is enabled. The Attack Simulator works but does not show any results when MFA is enabled, making it useless.
Note: If you want to ban known or weak passwords, I recommend looking at the Password Protection feature in Azure AD Premium.
Password Spray Attack
The Password Spray Attack is the same as the Brute Force Password (Dictionary Attack), except here is a single password used on multiple identities.

Conclusion
I like the idea that anyone can create a phishing campaign with a few clicks of a button. What I like most is that all data never leaves the tenant.
Unfortunately, the Attack Simulator needs a lot of work before it can be considered a proper awareness campaign service. If you want to ban well-known passwords from your tenant, I recommend the Azure AD Premium feature: Password Protection instead of testing passwords using the Attack Simulator.
Even though I have some concerns, the Attack Simulator is only one of many features in the Microsoft Office 365 ATP license. Looking at other elements like Safe Attachment, Safe Links, Anti-phishing policies, Reporting, and Automated investigation and response in the Microsoft Office 365 ATP license, I would recommend any organization to purchase Microsoft Office 365 ATP. Safe Attachment, Safe Links, Anti-phishing policies, and Automated investigation and response are a must-have, but I will go in-depth on these later.

