
[WARNING] This blog post is created when Microsoft Windows still came in a physical box with multiple installation disks.
Suppose you have a pay-as-you-go subscription in Azure. In that case, you might need to review who owns the Global Administrator role or who has owner permissions on that subscription in your tenant as a malicious user or attacker can hijack the subscription and make high costs at your expense. Since all activity logs are moved to the malicious user or attacker’s tenant, detecting this attack is, let us say, challenging. This blog post will briefly explain how attackers perform this attack.
Payment Information
Only a credit card or debit card is accepted when creating a pay-as-you-go subscription. Once you create the pay-as-you-go subscription, the payment information is attached to that subscription. So, suppose a malicious user or attacker moves the tenant’s subscription to a controlled tenant by the malicious user or attacker. In that case, the payment information is also moved over, including the activity logs. Once the subscription lives in the malicious user or attacker-controlled tenant, deploying resources comes at your costs, and you can not take it back. The result is losing all resources in that subscription, including very high costs if the attacker deploys resources.
Owner Permissions
It is possible to perform the attack if a malicious user or attacker gets owner permissions on a pay-as-you-go subscription. So be careful to give a guest user owner permission on a pay-as-you-go subscription. Since the guest user is out of your control, once the guest user gets compromised, an attacker can change the directory and move the subscription to an attacker controller tenant and deploy resources or mine crypto, which results in high costs.
Once a malicious user with the Global Administrator role or an attacker gets hold of a user with the Global Administrator role, a single click is needed to get owner permissions on all subscriptions within the tenant and perform the attack. The single-click option is the “Access management for Azure resources” within Azure Active Directory, elevating access to all subscriptions and management groups.
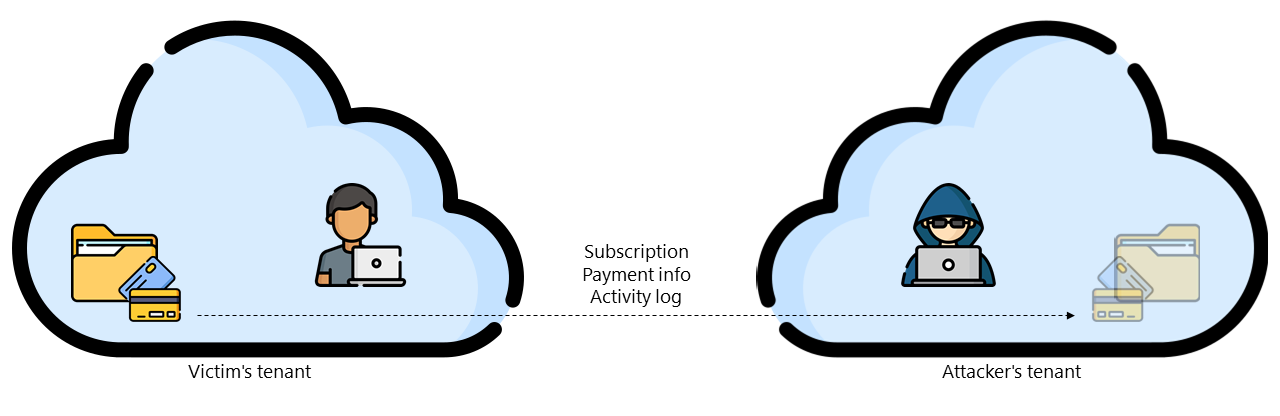
Once setting the owner permissions, the malicious user or attacker invites a user from the malicious user or attacker-controlled tenant and changes directory to move the subscription, including the payment information of the victim and the activity logs.
Conclusion
For me, it is mind-blown why Microsoft does not validate the payment information when moving the subscription to another directory. The activity logs move along with the subscription, so detection is challenging, but monitoring your identities, limiting the users with the Global Administrator role, and no owner permissions for guest users should lower the risk of a successful attack.