
[WARNING] This blog post is created when Microsoft Windows still came in a physical box with multiple installation disks.
A few months ago, I wrote a script that checks if a company uses Microsoft Defender for Identity. I then wondered if there is a way to identify if a company uses Microsoft Defender for Office 365. Safe Links, a Microsoft Defender for Office 365 feature, actively scans incoming URLs. So checking if Microsoft Defender for Office 365 scans the URL to identify Microsoft Defender for office 365 is manageable. This blog post will briefly explain how I identified if a company uses Microsoft Defender for Office 365 Safe Links, possibly without sending a single valid e-mail.
Microsoft Defender for Office 365
I do not want to detail what Microsoft Defender for Office 365 is, but an important feature to understand is Safe Links. Safe Links is a feature in Microsoft Defender for Office 365 that provides malicious URL scanning and time-of-click verification of links in e-mail messages and Microsoft Teams.
So if you sent an e-mail to a mailbox, URL scanning takes place by Microsoft Defender for Office 365 Safe Links. If you can identify if Microsoft performs the scan, you can determine if Microsoft Defender for Office 365 is enabled. So simply running an HTTP listener for incoming requests should do the trick.
Azure Function App
First, I thought running a simple HTTP server was enough, but then I had the idea to use a Function App since that already contains an HTTP trigger that I can use. If I could capture the incoming request, I could validate who is actively scanning the URL. But since I wanted to send myself an e-mail with the information, I thought it would be easier to use a Logic App instead.
Azure Logic App
When an HTTP request is received, the Logic App triggers. So capturing the request would be enough to get all the information I need. Unfortunately, I could not get the IP address of the initial request since the Logic App did not provide me with the correct information.
What I could do, though, is use an Azure Function App to send all the information I need to a Logic App and then send the e-mail.

Function Code
I ended up with a function using the HTTP trigger template. The HTTP trigger function runs whenever it receives an HTTP request, responding based on data in the body or query string. My function checks if the IP address to scan the URL is from Microsoft and sends a POST request to a Logic App.
using namespace System.Net
param($Request, $TriggerMetadata)
$IPAddress = $Request.Headers["x-forwarded-for"]
$UserAgent = $Request.Headers["user-agent"]
if($IPAddress -like "40.94.*.*") {
$MDODetected = "Yes"
}
Else {
$MDODetected = "No"
}
$params = @{'IP Address' = "$IPAddress";
'MDO Detected' = "$MDODetected";
'User Agent' = "$UserAgent";
} | ConvertTo-Json
Invoke-WebRequest -Uri 'https://prod-165.westeurope.logic.azure.com:443/workflows/<SNIP>' -Method POST -Body $params -ContentType 'application/json'
Push-OutputBinding -Name Response -Value ([HttpResponseContext]@{
StatusCode = [HttpStatusCode]::OK
Body = $params
})
Note: I identified Microsoft Defender for Office 365 Safe Links using the IP address, but technically you can identify any active scanning based on any header.
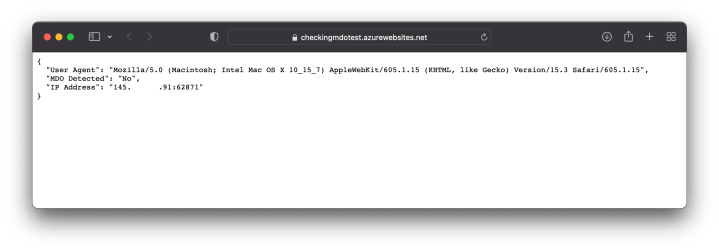
Pasting the Function App URL in a browser shows the following information.
Sending an e-mail
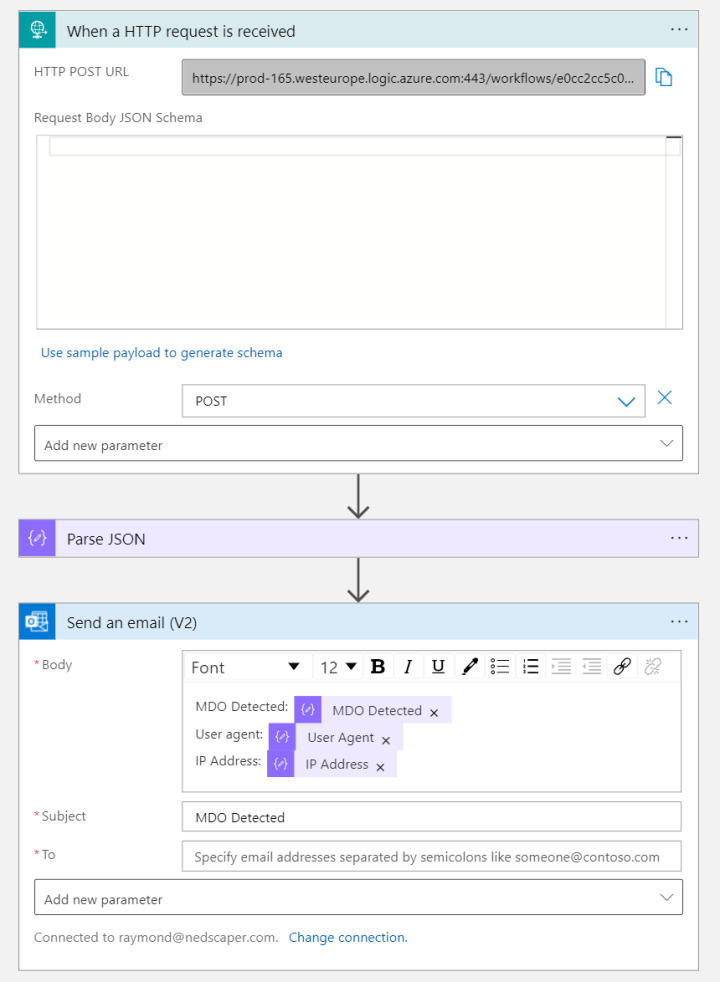
Now that we identify who is scanning the URL by capturing the GET request, we can forward it to a Logic App and send ourselves an e-mail with the information we need.
We can trigger the Logic App with a POST request, parse it to JSON, and send the information from the JSON parsing using an e-mail. Here is a screenshot of the Logic Apps steps.
We have to send the Function App URL to an e-mail address and see if Microsoft scans the URL. Sending the Function App URL is enough to get the information needed to identify if Microsoft scans the URL.
Note: To ensure that Microsoft scans the URL, you need to use a URL shortener and send the shortener URL to a mailbox. More information about that in a future blog post.
An e-mail to a non-existing mailbox also does the trick, depending on the configuration. So first, try to send an e-mail to a non-existing mailbox. If it identifies as “Microsoft Defender for Office 365 Identified,” you know Microsoft Defender for Office 365 is running, and you do not have to send an e-mail to an existing mailbox to be more stealthy.
Conclusion
Using this technique makes it possible to also identify other e-mail scanning services, but my main goal was to identify Microsoft Defender for Office 365, and it worked.